Protecting Digital Signatures: It’s About Time


As part of Solutions Review’s Premium Content Series—a collection of contributed columns written by industry experts in maturing software categories—Mrugesh Chandarana, the Director of Product Management at HID Global, shares some insights into the value and importance of protected and verifiable digital signatures.
 The use of “digital signatures” has exploded during the pandemic. Around the globe, people have changed how they travel, transact, and work. In the manufacturing sector, organizations have gravitated to hybrid work environments. In all of these cases, digital signatures are being used to protect digital interactions and digital assets, from documents to software code. Unfortunately, all of these digital assets remain at risk since the signature’s certificate may have expired or been revoked. Fraudsters can make these certificates appear as though they were still valid. But their changes and forgeries can be combatted using time stamping services that bring trust to digital signatures.
The use of “digital signatures” has exploded during the pandemic. Around the globe, people have changed how they travel, transact, and work. In the manufacturing sector, organizations have gravitated to hybrid work environments. In all of these cases, digital signatures are being used to protect digital interactions and digital assets, from documents to software code. Unfortunately, all of these digital assets remain at risk since the signature’s certificate may have expired or been revoked. Fraudsters can make these certificates appear as though they were still valid. But their changes and forgeries can be combatted using time stamping services that bring trust to digital signatures.
The Risk Timeline
A time-based workflow associated with digital signatures is best understood by reviewing a traditional ink signature workflow. Whenever a legal document is signed, a notary is typically present. The notary’s job is three-fold. First, there must be verification of the person’s identity who is signing. Second, the notary must validate the date and time of the signature. After these two processes are completed, the third step is recording the signature in a logbook with the date and time of the transaction and a thumbprint.
A version of this flow is used in the digital world. After a document is signed with a public key infrastructure (PKI)-based digital signature, there is a non-repudiation step. Non-repudiation provides proof of the data’s origin and integrity, making it difficult for the party to a contract or communication to deny the signature’s authenticity or that the message was sent at all. But this repudiation step cannot necessarily be trusted.
When a PDF document is digitally signed with a PKI-based certificate, the information about the person signing is added, along with the date and time of the signature. However, this date and time are based on the computer’s local time, which can be changed. This makes it easy for someone to manipulate or forge the signature’s date and time fraudulently. The only way to trust the digital signature is to ensure that its timestamp can be authorized.
Widget not in any sidebars
How Trusted Time Stamping Works
Trusted digital identities are needed for various applications ranging from authentication and data encryption to document and code signing. PKI digital certificates are used to create them. To establish proof of these signatures’ existence at an instant of time, the Internet Engineering Task Force (IETF) created the PKI Time-Stamp Protocol (TSP). When this protocol is used, it is possible to combat digital certificate forgery and prevent unauthorized use of revoked certificates and simplify time-based compliance record-keeping. The use of trusted timestamps also strengthens legal cases and proves the long-term validity.
For instance, antivirus updates can be secured using signatures with a trusted timestamp. Without a timestamp, signatures will expire or invalidate when the certificate expires or is revoked. End-users will be warned that they should not trust the code. But with a timestamp and long-term validation, the signature will still be trusted since the signing certificate was valid when the signature was applied.
Accurate and trusted timestamps are applied to a digital signature by a Time Stamping Authority, which must meet RFC 3161 requirements established by the IETF. The RFC 3161 Time Stamp Protocol proves no tampering with the data. Using a Time Stamping Authority while signing a document or code prevents tampering with the Timestamp.
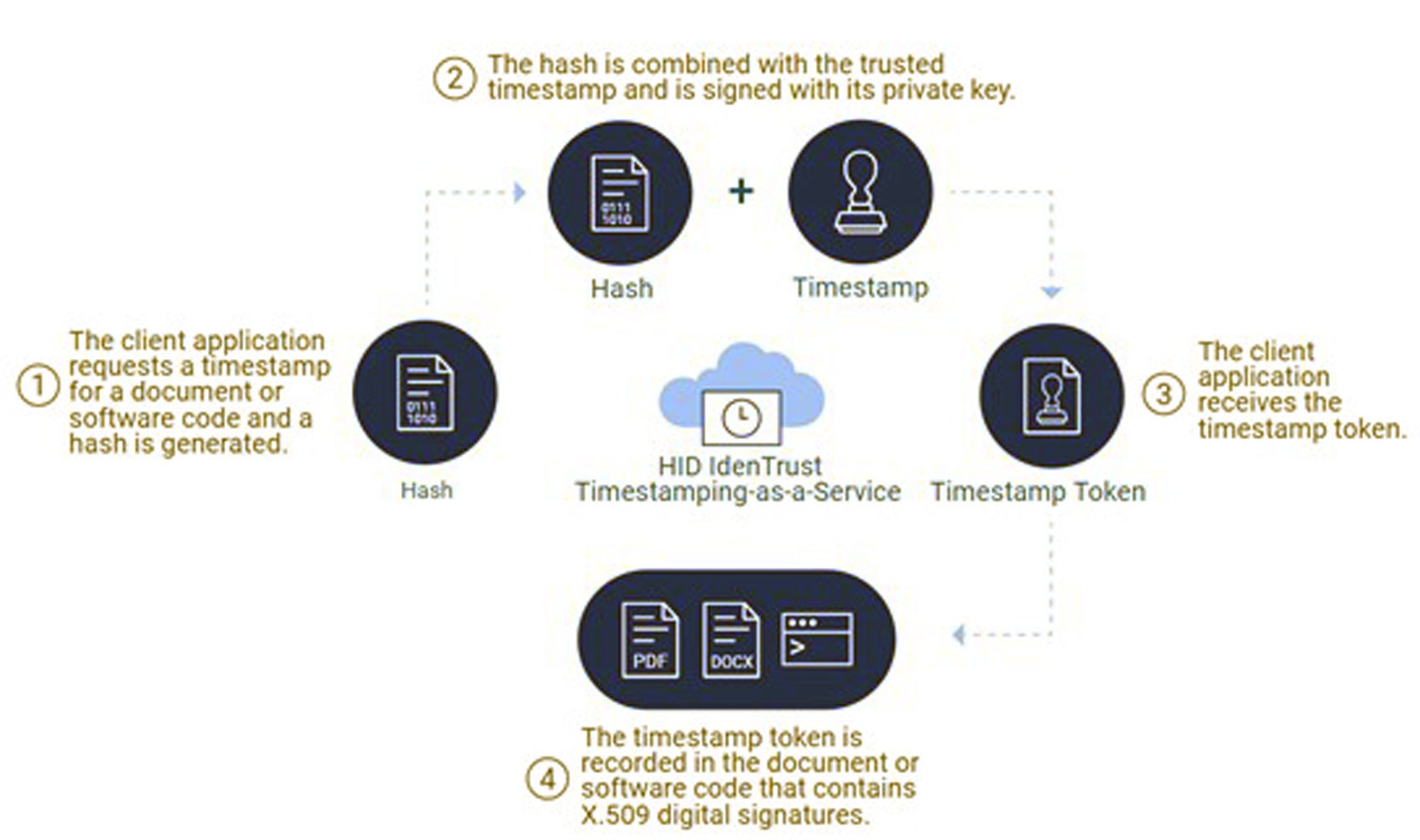
The process is as follows: First, the client application (Microsoft Authenticode or Signtool, as examples) creates a hash of the document or code file. It has a unique identifier of the data or file that must be timestamped. This hash is sent to the Time Stamping Authority, which combines the hash of the file with a trusted timestamp and signs it with a private key. A timestamped token is then created and returned to the client. The timestamp token contains the client application’s information to verify the timestamp later. The process concludes with recording the timestamp token within the file.
When the resulting timestamped data or file is later opened, the client application will use the Time Stamping Authority’s public key to validate that the timestamp came from a trusted Time Stamping Authority and re-calculate a hash of the original data. This new hash is compared to the created hash. The hash check will fail if any changes have been made to the data since the timestamp was applied, this hash check. Warning messages will also be shown saying that the data has been altered and the timestamp should not be trusted.
This process must be executed at very high throughput rates in many use cases. An example is antivirus signature file signing or firmware signing – millions of timestamps might need to be applied each week. Trusted time stamping service providers make this easier, as they provide enterprises with a high-availability cloud-based platform for embedding timestamps. These timestamps can be embedded in any software application, documents, or digital file. Any manipulation of the timestamp file is after the signature and timestamp are applied causes a hash value mismatch that breaks the file’s seal and alerts the user that the file can no longer be trusted. It is no longer in its original state, and the data is altered.
Trusted timestamps are vital to the integrity of digital signatures because they are applied using independently verified and Coordinated Universal Time (UTC) sources. Because they are not subject to tampering like a local system clock, they foster certainty about applying a digital signature. Trusted time stamping will continue to see growing demand among users to verify the date and time of their electronically or digitally signed documents, code, and other files. Doing so can prevent forgery while also creating longevity for these digital signatures, even after expiration, through long-term validation and non-repudiation of their time and date.
Widget not in any sidebars



















