Improper Hard Drive Disposal Could Be a Million-Dollar Mistake


Solutions Review’s Expert Insights Series is a collection of contributed articles written by industry experts in enterprise software categories. In this feature, Secure Data Recovery‘s Yevgeniy Reznik offers commentary on improper hard drive disposal and best practices to know.
 According to the FBI’s most recent Internet Crime Report, the cost of cyber-crime is rising. Some experts speculate that the enhanced posture of corporations and other large organizations is causing malicious actors to pivot toward small and medium-sized businesses.
According to the FBI’s most recent Internet Crime Report, the cost of cyber-crime is rising. Some experts speculate that the enhanced posture of corporations and other large organizations is causing malicious actors to pivot toward small and medium-sized businesses.
While most users and IT departments are aware of well-publicized cyber-crimes, such as phishing or ransomware, they are often unfamiliar with a cheaper, lesser-known method of accessing compromising data:
Acquiring old hard drives or solid-state drives that have not been sanitized.
Dangers of Improper Hard Drive Disposal
Improper hard drive disposal can have devastating consequences. Companies that relinquish control of devices still storing sensitive data could encounter several problems.
The immediate concern is containing the data breach. The average cost of a data breach in the United States in 2022 was $9.44 million. That staggering sum jeopardizes the survival of most small businesses that suffer an attack. In addition, if mishandling hard drives exposes customers’ personal information, organizations could incur significant legal liabilities. These expenses do not even consider the reputational damage that occurs when a business experiences a data breach.
So, what is the likelihood of obtaining confidential information from discarded drives?
Greater than one would expect.
How Far $100 Will Go
We decided to explore the issue at Secure Data Recovery.
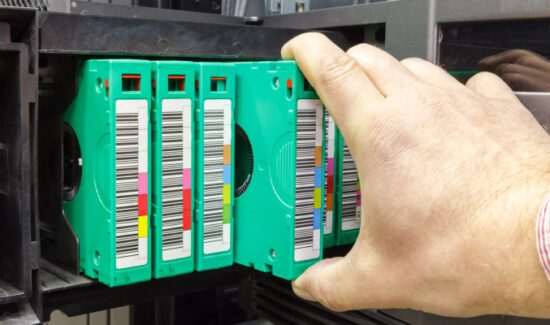
For less than $100, we acquired fourteen hard drives.
Sellers listed the devices as available for parts or dead. Purchasing donor drives facilitates our hard drive repair operations. However, in this instance, we examined whether the sellers sanitized these devices before shipping them.
Our engineers discovered that those parties sanitized a single drive within the sample. The remaining thirteen disks were not. Out of the thirteen unsanitized devices, we recovered all the stored data from seven. Most hard drives did not require extensive repairs to retrieve their files.
In the end, we recovered 216,109 files. The final collection of data included 187,630 images, 19,223 documents, 5,931 audio files, and 3,325 videos. Our technicians extracted four mailbox databases as well.
To reiterate, we spent an average of $7.06 on these devices. Yet malicious actors could attain financial statements, medical records, trade secrets, log-in credentials, and other critical data.
Achieving data protection is impossible without proper data destruction procedures.
6 Best Data Destruction Practices
Following the best data destruction practices gives businesses the best chance to prevent data breaches. Different destruction methods offer different degrees of protection. The ideal approach depends on each organization’s circumstances. Companies storing more personal or private data should prioritize the most effective options.
Despite concerns over cost, data destruction is more economical than recovering from a crippling attack or mishandling incident.
Shredding
Hard drive shredding is one of the most popular forms of data destruction. Operators run the device through a media shredder. The shredder tears the hard drive’s platters into small, irregular pieces. At that point, its data is unrecoverable.
Disintegrating
Similar to shredding, disintegrating leaves the device in an unrecognizable state. Rather than cutting platters, disintegrators reduce hard drives to a fine residue. Though more expensive, enterprises with large amounts of data tend to select disintegration.
Degaussing
Degaussing is an efficient means of hard drive destruction. A degausser is a machine or wand that scrambles the hard drive’s magnetic field. The demagnetized device is unreadable and unusable.
Melting
Melting is the process of dipping a hard drive in harmful chemicals. The chemicals corrode the drive’s mechanical components and strip the film from its platters. Despite its effectiveness, melting is the most dangerous method. Therefore, it is not recommended.
Drilling
Drilling is a common choice for individuals or organizations that need a cost-effective deterrent. Puncturing the device’s case with a drill ruins its internal components, including the platters. Drilling a random pattern through the drive’s platters delivers the best results.
Overwriting
Overwriting saved data is a potential DIY method. Users can overwrite the hard drive’s contents through full formatting or a data erasure program, such as DBAN. Adhering to the Department of Defense’s three-pass standard provides greater data protection.
Safe Data, Safe Future
Data is one of an organization’s most valuable assets.
That makes safeguarding it essential. While it is in use and once it reaches the end of its lifespan.
Too often, businesses view data destruction as an avoidable cost instead of an investment. However, the financial and reputational ramifications of a data breach are impossible to ignore.
There have been extraordinary advancements in RAID and hard drive recovery in the past decade. The state-of-the-art tools and techniques of data recovery services have made once-complicated recoveries routine. But a growing number of cybercriminals are gaining access to the same equipment and knowledge.
Businesses should assess their threats and address their weaknesses.
Failing to implement proven disposal procedures could inflict irreparable damage.
- Improper Hard Drive Disposal Could Be a Million-Dollar Mistake - April 28, 2023