Is Blockchain the Future of Cybersecurity?
In the eyes of data experts, blockchain has become a panacea for digital age woes. Banking , finance, real estate, education, social media—blockchain is expected to facilitate or outright revolutionize all of these industries’ online operations. Already vital to the functionality of Bitcoin and other cryptocurrencies, cybersecurity professionals now look to blockchain to fundamentally transform their solutions and improve their platforms. But how can one technology be so versatile as to do all this? And does blockchain truly represent a new era in InfoSec?
Widget not in any sidebars
What is Blockchain?
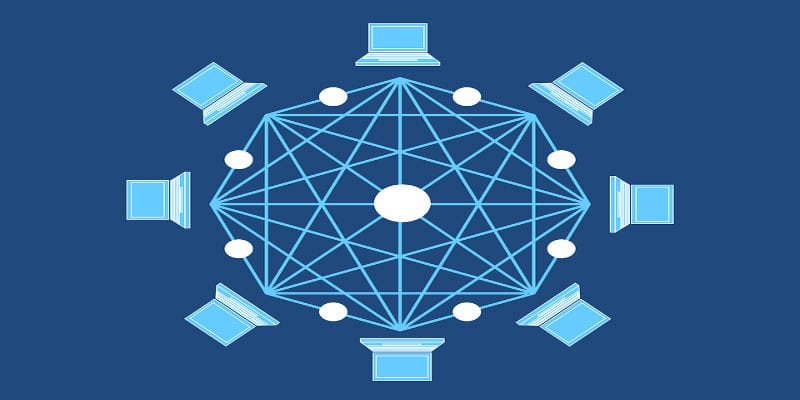
Invented by an individual or organization under the pseudonym Satoshi Nakamoto, Blockchain functions as a kind of decentralized database operating in a large-scale, peer-to-peer fashion. This disparate database can be updated by anyone in its network; the data is simultaneously stored and continually updated across multiple interconnected endpoints. In the simplest language, blockchain resembles a spreadsheet accessible by anyone that anyone can update, and the changes to which everyone will see accurately.
Indeed, accuracy of information serves another fundamental aspect of blockchain technology. In order to keep the data consistent and uncorrupted across so many endpoints and users, blockchains automatically encrypt all the actions in a file or on a digital object into the base code of that file or object. Since this encryption becomes a fundamental part of the code itself, it can’t be removed or altered anonymously or covertly, which makes all of the activity and the users transparent and immediately apparent.
This explains how Bitcoins can be used as legitimate currency without worry of a user reusing their currency or using currency they do not have: blockchains record who is the owner of a bitcoin, records any transactions the user conducts using that bitcoin, and update the bitcoin to reflect the new ownership with an encryption to preserve its integrity.
What Makes Blockchain So Useful for InfoSec?
InfoSec professionals fawn over blockchain because it solves many of the problems plaguing the industry over the past few years. The distributed database model prevents hackers from tampering with data directly, as it does not provide a singular target for an attack. This factor places it high above more centralized and more easily available databases. Further, blockchains remove the anonymity that benefits so many hackers by publicly recording all user actions automatically and preventing alterations to that record.
More concretely, solutions providers are looking to blockchains as a new tool in their identity management solutions. Because it can securely record and store user data across disparate sources, blockchains can be used to create a unique public key for each person; these in turn can authenticate users securely without the use of a traditional (and increasingly insecure) password and without the fear of hackers using false certificates to pose as a legitimate user.
Blokchain’s apparent success in maintaining data integrity feeds into the overwhelming optimism surrounding it. While Bitcoin has been plagued by robberies, the underlying blockchain infrastructure has remained secure. Estonian vendor Guardtime has already used blockchains to secure all of their country’s health records—information for over one million people. Other vendors are exploring blockchain’s authentication capabilities with reported success.
Above all, blockchains are praised for removing the human error component in data integrity by removing the need for easily leaked, easily forgotten, and frequently introduced passwords.
Flawless Security?
The optimism around blockchains seems universal—even the Pentagon has expressed interest in it—but this should be a word of caution rather than an encouragement for blind trust. Blockchain has survived for nearly 10 years without being hacked, true, but the longer a technology stays in the digital public, the more time hackers have to crowdsource and crack the problem; very little stays permanently secure in this field. Innovation is as much an enemy as a friend.
Additionally, human error continues to be humanity’s most persistent problem, stubbornly refusing to be solved no matter what technology is thrown at it. Even in the new public key conception of security solutions providers project from the success of blockchain leaves users the ability to give out their public key or to forget to remove permissions from the public key of a disgruntled ex-employee.
On a more technical level, blockchains are designed to be permanently public to prevent anonymous actions; which means that potentially sensitive information is left exposed. As stated by Netspective CEO Shahid Shah in an interview with Security Intelligence, “blockchain is more about guaranteeing the integrity of data rather than keeping data private, [so] it’s not likely to reduce data breaches.”
So even with blockchain technology, leaks will continue. but hackers will be unable to maliciously change the identity data an enterprise maintains. And that may yet prove a crucial win in our war against hackers.
Other sources can be found here.
Widget not in any sidebars


















