How to Embrace the Basics of a Secure Storage and Backup


Solutions Review’s Contributed Content Series is a collection of contributed articles written by thought leaders in enterprise technology. In this feature, Apricorn US Managing Director Kurt Markley offers commentary on how to embrace the basics of secure storage and backup.
With the ever-evolving cybersecurity landscape, it’s easy for organizations to get caught up in the hype of new products and tools. After all, cybersecurity is, according to Gartner, a $172 billion business (2022). Despite the fear, uncertainty, and doubt prompting organizations to over-buy, it’s important not to overlook the basics of cybersecurity, especially when it comes to protecting your data.
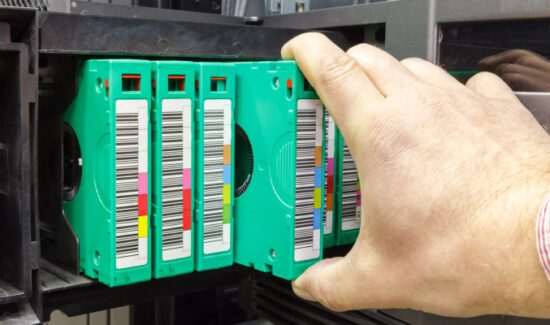
With the ongoing scourge that is ransomware continuing to wreak havoc across enterprise landscapes, one of the most critical aspects of cybersecurity for these businesses is backup and recovery. Having a solid backup strategy in place can help minimize the damage caused by a cyber-attack or natural disaster. But where should you store your backups? The answer is simple: in a variety of places, including the cloud and encrypted external hardware storage devices.
Secure Storage &Backup
Encryption Should be Mandated
It should go without saying that encryption is a critical aspect of protecting your data. By encrypting all of your backups, you can ensure that even if your storage devices fall into the wrong hands, the data cannot be accessed without the decryption key.
Encryption is a generally accepted best practice for storing data. According to the Apricorn 2022 IT Security Survey, 82 percent of respondents said that encryption should be required to secure USB storage devices. The issue is that not every best practice is being followed. In that same survey, only 34 percent say that encryption is mandated within their organizations to protect data on the move.
When considering backup and storage strategies, enterprises have to simply keep encryption on the table. It is one of the best ways to ensure only the right people have access to your critical data and is a simple practice – that works – to put in place.
As Simple as 3-2-1
The 3-2-1 rule is a well-established best practice for backup and recovery. It involves keeping three copies of your data on two different types of media, with one copy stored off-site. While cloud-based storage is useful, easy and important, your data should never be stored in the cloud alone. We saw what happened in 2021 when the OVHcloud SBG2 data center in Strasbourg, France burned down. Not only did the fire destroy servers storing data for hundreds of organizations, but, because the company stored backup servers in the same building, customers lost all their data. In fact, in March 2023 OVHcloud was ordered to compensate two customers because it was unable to fulfill its promise to provide backups should the original data be lost.
As noted, one of the biggest threats to enterprise data is ransomware. In fact, according to the same Apricorn survey, most respondents (93 percent) say they have a ransomware readiness plan, but significant knowledge gaps exist regarding adequate backup and cyber resilience practices. Only one in three back up to both the cloud and encrypted hardware storage devices, even though 82 percent want their organizations to require encrypted hardware USB usage. Additionally, only 20 percent back up in real-time, and only 18 percent employ the long-established best practice for backup: the 3-2-1 method.
Choosing the Right Backup Mediums
There’s no question that the convenience and scalability of the cloud make it a popular choice for storing enterprise data. That’s not going to go away. But to support the cloud and ensure enterprises are embracing the 3-2-1 rule, encrypted external hardware storage devices, like USBs or hard drives, are a critical component of a complete backup and recovery strategy. They offer a secure, portable, and convenient way to store your backups off-site, ensuring that your data is protected even if your primary storage is compromised.
However, it’s important to note that not all encrypted external hardware storage devices are created equal. When selecting a device, look for one that offers strong encryption, such as AES-256, and has been independently certified by organizations like FIPS, the National Institute of Standards and Technology (NIST), or Common Criteria.
Practicing Proper Data Hygiene
Data hygiene is no one’s favorite thing to do and might be tedious work, but it’s far less dreary than trying to recover from a successful ransomware attack. Proper data hygiene encompasses performing regular data management audits to identify vulnerabilities, safeguarding practices, and attack vectors. By understanding where the gaps in your data protection strategy exist, you can better build plans to restore operations after an incident.
For example, consider performing regular backups of your data to ensure that all your information is secure. In addition, establish proper data retention policies to determine how long to keep data, what data to retain, and how to securely dispose of data that is no longer needed.
Another important step in data hygiene is to establish strong password policies. This includes requiring users to create strong passwords that are difficult to guess, and to change their passwords regularly. Multi-factor authentication can also be implemented to further protect your data.
At the end of the day, while there may be many flashy cybersecurity products and tools out there, the basics are still around for a reason: they work. A solid backup and recovery strategy that embraces a 3-2-1 strategy, ensures encryption of data and gives credence to data hygiene can help minimize the damage caused by a cyber-attack or natural disaster. Don’t wait until it’s too late – invest in the basics now to protect your enterprise’s data in the future.
- How to Embrace the Basics of a Secure Storage and Backup - August 17, 2023