5 Reasons Automating Identity Lifecycles Will Make Your Life Easier
Here’s an understatement: today’s IT leaders are busy people.
Sure, the concurrent explosions of mobility and cloud-enabled technology have made your organization faster, more efficient, and more productive, but they’ve also muddied the waters—the clean line we’ve drawn between the world we live in and the one we work in has blurred.
The glut of mobile devices in the workplace, the advancement of cloud computing, the evolutions of distributed systems, data, and networks—all these things are a boon, but they’ve also created a flood of security challenges for IT professionals.
Foremost amongst those challenges is The Identity Lifecycle Management Problem, AKA the “all I do these days is answer helpdesk calls and manually provision and deprovision user access” problem.
At first, most IT organizations were able to implement basic, manual processes to address this problem. Maybe you were able to write a script that processes .CSV files from HR into Active Directory, and maybe that worked for a while. But the aforementioned proliferation of SaaS apps means you’re now required to provision access to both internal and external applications. Each app requires its own onboarding and offboarding events, and each one has its own unique set of authorization mechanisms—things get complicated, fast.
For the new user Many IT admins typically spend roughly 30 minutes of IT admin time per provisioning request—that adds up quick.
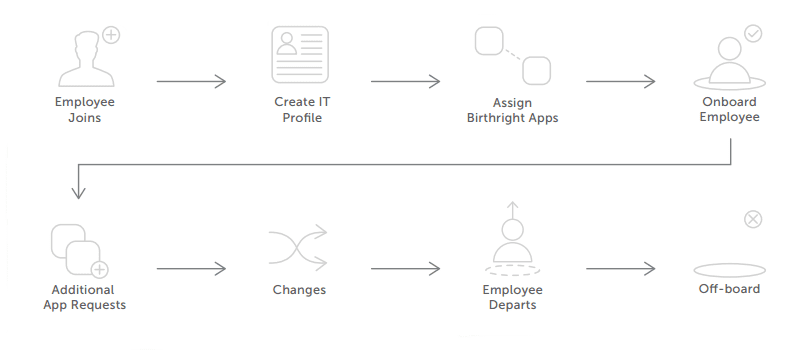
But there’s an easier way. By automating how users are created, how identity and access is managed as users change roles, and how you handle the clean-up after users leave you can save time, money, and headaches, all while creating a more secure environment for your corporate resources.
There are 5 big reasons to make an investment in a serious tool to automate identity lifecycle and provisioning:
- Creating and changing users in applications is time-consuming.
- Your process for coordinating with HR feels like it’s from 1998.
- Different teams have different business processes, and it’s hard to keep up.
- It’s not easy for end users to set up their device or get access to niche apps.
- You don’t have full control over business apps, yet you’re responsible for security.
 To get more detail on the top 5 reasons to automate identity lifecycle and identity administration, check out this recent whitepaper from IDaaS vendor Okta. In their report, Okta breaks down in detail the 5 top reasons listed above, and discusses how you can build a solid foundation for future cloud-first, mobile-first IT with automated lifecycle management. Click the image here for a free, full-length copy of the report.
To get more detail on the top 5 reasons to automate identity lifecycle and identity administration, check out this recent whitepaper from IDaaS vendor Okta. In their report, Okta breaks down in detail the 5 top reasons listed above, and discusses how you can build a solid foundation for future cloud-first, mobile-first IT with automated lifecycle management. Click the image here for a free, full-length copy of the report.

















