Key Findings: Gartner’s Access Management Critical Capabilities
Analyst house Gartner, Inc. released its Critical Capabilities for Access Management, Worldwide report—a companion resource to their popular Magic Quadrant report. Used in conjunction with the Magic Quadrant, the Critical Capabilities Report is a vital additional resource which can assist buyers of access management solutions in finding the products that fit best their enterprises’ IT environments.
You can read the full Gartner Access Management Critical Capabilities report here, courtesy of Centrify.
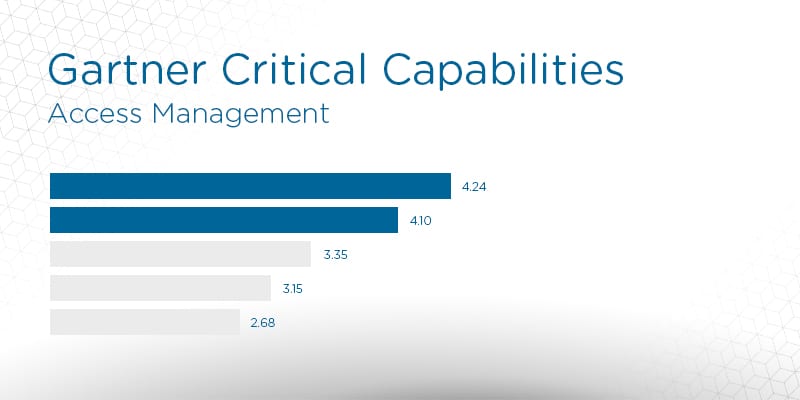
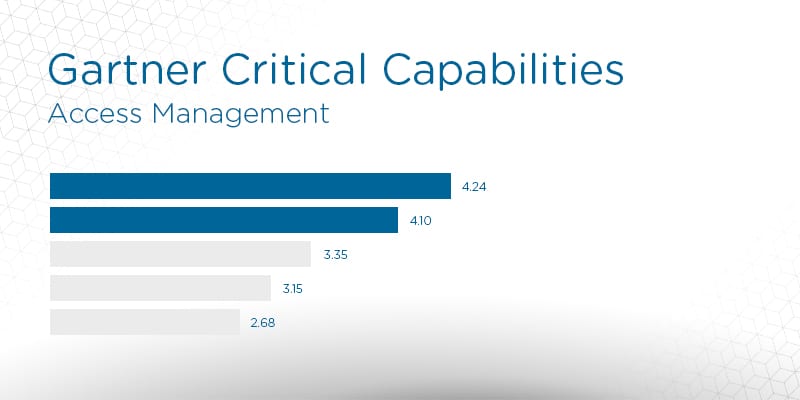
Gartner defines Critical Capabilities as “attributes that differentiate products/services in a class in terms of their quality and performance.” Gartner rates each vendor’s product or service on a five-point (five points being best) scale in terms of how well it delivers each capability. Critical Capabilities reports include comparison graphs for each use case, along with in-depth descriptions of each solution based on the various points of comparison.
The study highlights the 15 vendors Gartner consider the most significant in the access management software sector and evaluates them against 10 critical capabilities and 3 distinct use cases prevalent in the market space.
The vendors in the Gartner Access Management Critical Capabilities report are Atos (Evidian), Auth0, CA Technologies, Centrify, ForgeRock, IBM, i-Sprint Innovations, Micro Focus, Microsoft, Okta, OneLogin, Optimal IdM, Oracle, Ping Identity, and SecureAuth.
The Access Management Critical Capabilities listed in the report includes session management, social identity support, SaaS application enablement, event logging and reporting, and the ability to administer users and partners.
The editors at Solutions Review have read the Access Management Critical Capabilities report and pulled out two key takeaways. They are:
IDaaS Disrupting Traditional Distribution
One of Gartner’s most prominent findings in the Access Management Critical Capabilities report is the increasing prominence of IDaaS as the preferred delivery method for AM technology. IDaaS is already outpacing traditional software-based AM products for new purchases. Gartner also predicts by 2022, IDaaS will be the chosen delivery model for more than 80% of access management deployments (it is only around 50% at time of writing).
Legacy AM Solutions Are Ossifying
Even with most enterprises already secured with an AM product, Gartner states there are still plenty of greenfield purchases and legacy solution replacement purchases. While modern IDaaS vendors can still struggle supporting legacy applications or enforcing session management capabilities, Gartner states that part of the problem is ossifying corporate networks.
To alleviate this, Gartner suggests enterprises conduct an inventory of the applications “in scope” for their access management, examining their supported use cases and user constituencies. If applications do not support standards based-SSO, Gartner recommends diving into the costs and effort needed to switch to applications supporting those standards.
You can read the full Gartner Access Management Critical Capabilities report here, courtesy of Centrify.
Widget not in any sidebars




















