Infographic: The 5 Phases of a Ransomware Attack


“If you know the enemy and know yourself, you need not fear the result of a hundred battles. If you know yourself but not the enemy, for every victory gained you will also suffer a defeat. If you know neither the enemy nor yourself, you will succumb in every battle.” ― Sun Tzu, The Art of War
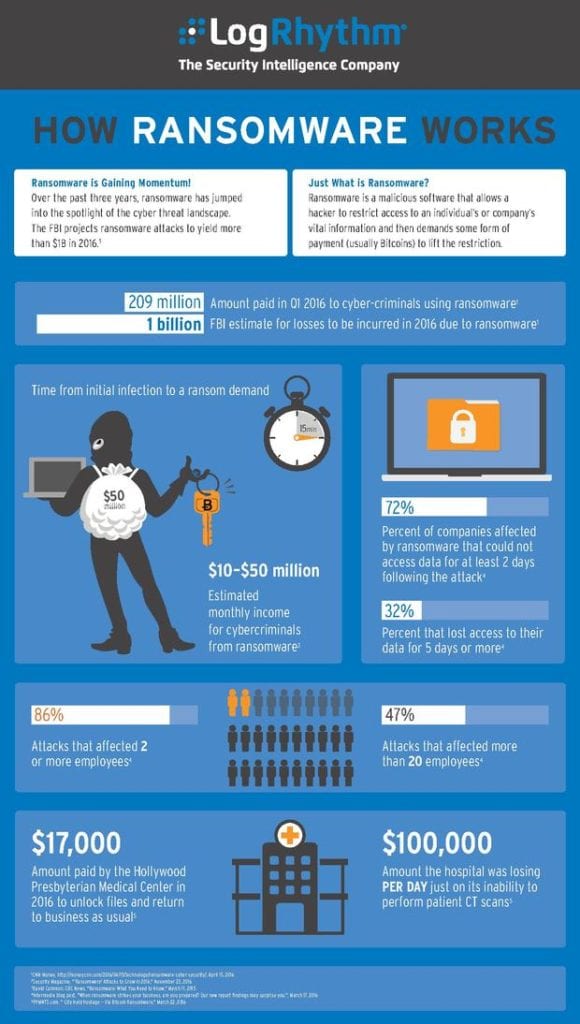
Ransomware is rapidly becoming the foremost cybersecurity threat in the world. In 2015, people and companies in the United States paid $325 million to ransomware wielding cyber criminals. Additionally, a number of high-profile attacks made headlines in mainstream media outlets revealing the depths of the continued crisis.
Ransomware losses continue to skyrocket in 2016— in April, CNBC estimated the cost of ransomware at around $200 million in the first three months of 2016 alone, and the FBI projects ransomware attacks to cost businesses more than $1 billion in 2016.
Despite these shocking numbers, many consumers and businesspeople know frighteningly little about the looming malware threat. In fact, 43% of consumers in the US and Canada have never even heard of ransomware, according to a recent report from Kaspersky Labs.
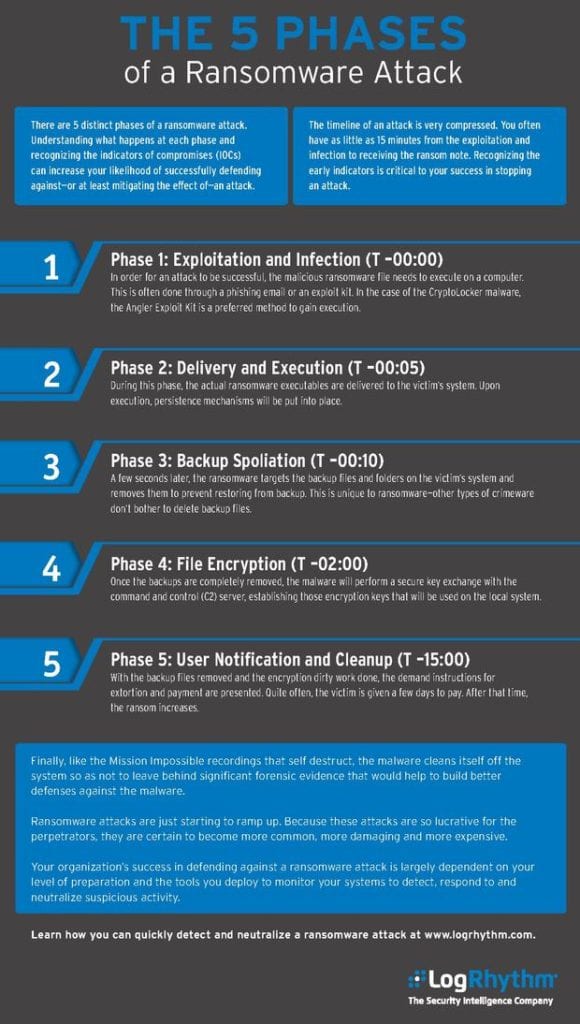
If you’re reading this, you hopefully have some idea of what this malware species is, but do you understand how it works? Do you know what it’s likely to target and how it can subvert your own strategies to achieve its illicit goals? Critically, do you know how to get rid of it when it does strike?
They say the first step to victory is to know your enemy, so check out this handy infographic from SIEM solution provider LogRhythm; this image breaks down the what, how, and why of attacks and explains the five phases of the average ransomware attack. You can also learn more about LogRhythm and other SIEM vendors in our 2019 Buyers’ Guide.
Widget not in any sidebars




















