LogRhythm Releases Cloud-Based Threat Analytics Tool: LogRhythm CloudAI
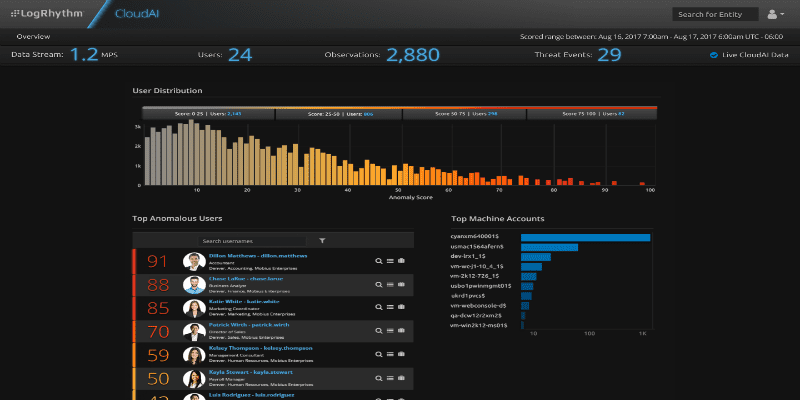
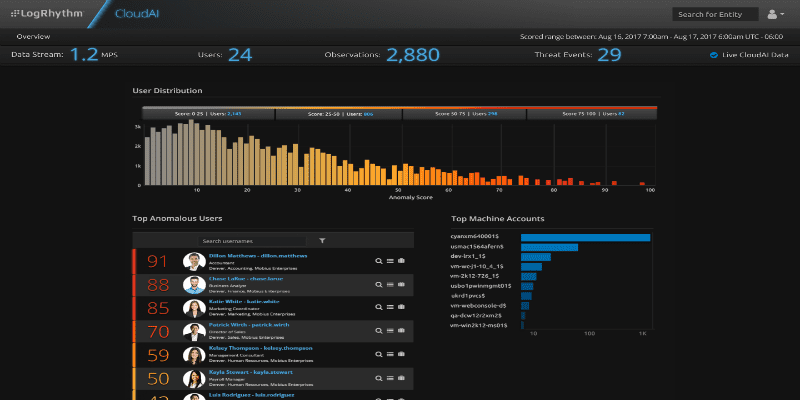
SIEM and network monitoring solutions provider LogRhythm has a new cloud-based security analytics offering that is available as a fully integrated, add-on subscription service for the LogRhythm Threat Lifecycle Management Platform. Dubbed LogRhythm CloudAI, the new tool is focused on extending and enhancing LogRhythm’s existing user and entity behavior analytics (UEBA) capabilities by using artificial intelligence to detect advanced threats that employ unknown attacks and unknown methods and provide security teams immediate visibility into emerging and active user-based threats.
According to a release, LogRhythm CloudAI is powered by analytics and artificial intelligence techniques such as unsupervised machine learning, giving it the capability to detect emerging and advanced threats based on deep analysis of observed activities and behavioral shifts. To continuously enhance accuracy, LogRhythm CloudAI employs supervised machine learning and real-world feedback from LogRhythm’s global customer base..
“We believe artificial intelligence holds the promise to transform the accuracy of threat detection and automate broad categories of work within the SOC,” said LogRhythm CTO and Senior Vice President of Research & Development, Chris Petersen. “CloudAI has the potential to be a leap forward in the evolution of the AI-enabled SOC, giving organizations the capability to significantly improve the efficacy of their threat detection and response programs.”
CloudAI’s UEBA capabilities work in conjunction with LogRhythm’s existing scenario-based analytics and library of threat models, which are designed to detect the known tactics, techniques and procedures of threat actors.
“CloudAI has allowed us to become more successful in detecting user based threats that would have previously eluded us without the benefit of blind luck or manually sifting through an avalanche of forensic data,” said Prologis Senior Security Architect, Tyler Warren. “My team simply can’t afford to waste time pursuing false positives. CloudAI does the time-consuming work for us, allowing us to focus on the things that really matter.”
You can find out more about LogRhythm CloudAI here.
Widget not in any sidebars




















