Key Takeaways: Forrester’s 2016 Endpoint Security Suites Wave Report
Cambridge-Ma based analyst house Forrester Research has released the latest iteration of its flagship Wave report for Endpoint Security Suites.
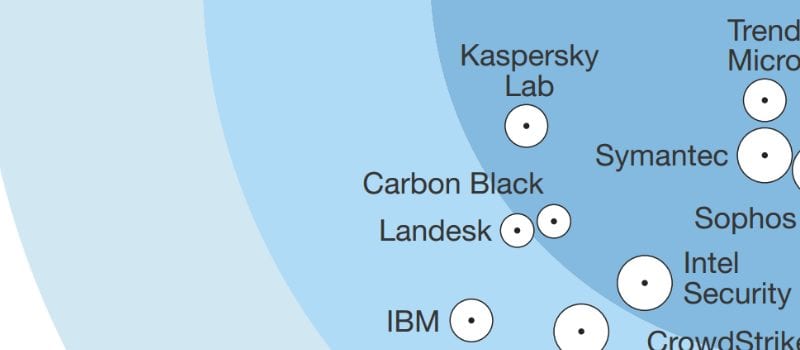
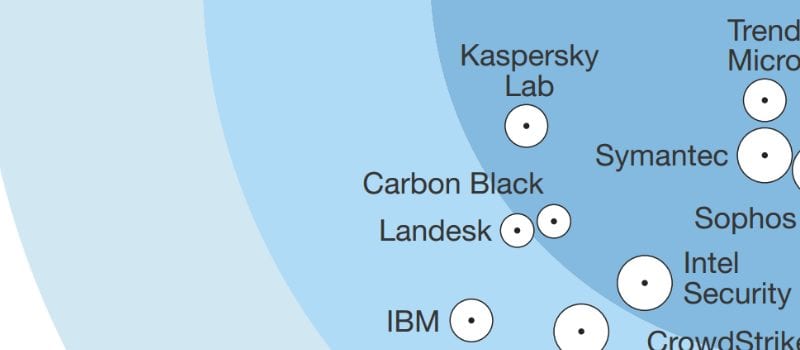
In their 25-criteria evaluation of Endpoint Security Suite providers, Forrester researchers Chris Sherman, Christopher McClean, Salvatore Schiano, and Peggy Dostie identified the 10 solutions providers that they consider most significant in the category — Bromium, Carbon Black, CrowdStrike, Cylance, ESET, IBM, Intel Security, Invincea, Kaspersky Lab, Landesk, Palo Alto Networks, SentinelOne, Sophos, Symantec, and Trend Micro— then researched, analyzed, and scored them.
The Wave report details their findings and examines how each vendor meets (or falls short of) Forrester’s evaluation criteria and where vendors stand in relation to each other.
In order to help security and risk (S&R) professionals select the right partner for their Endpoint Security needs, The Forrester Wave Report also outlines the current state of the market and separates the top providers into Leaders, Strong performers, and Contenders.
Forrester’s Wave Reports also include a grid chart with ratings on vendor’s current offerings, strategy, and market presence.
At Solutions Review, we read the 19-page report, available here, and pulled a few of the most important takeaways.
Big Vendors Lead The Way
Forrester’s research found a stratified market in which Trend Micro, Sophos, Symantec, Kaspersky Lab, Intel Security, and Carbon Black are Leaders, Cylance, Landesk, CrowdStrike, ESET, Palo Alto Networks, IBM, SentinelOne, and Invincea offer competitive options, and Bromium lags behind.
Forrester praised Carbon Black’s Cb Response and Cb Protection products for offering a strong balance of prevention, detection, and remediation functions “without relying on signature blacklists”, and lauded Intel’s McAfee Complete Endpoint Protection product for it’s broad security capabilities, which are well integrated with a common policy engine and intelligence stream. On the other hand, vendors on the opposite spectrum of the ‘Wave’ were criticized for lacking ancillary endpoint security technologies that enterprise buyers require.
Three Capability Sets to Consider
In 2016, Endpoint Security is a mature, yet highly fragmented market. Point solutions, security suites, “next gen” and legacy vendors all compete for their slice of the security budget pie.
To cut through the noise, Forrester suggests that buyers categorize vendor capabilities into three ‘core needs’: attack prevention, detection, and remediation.
“Before making any new purchases,” says Forrester “consider a vendor’s ability to meet each of these needs.”
Threat Analytics a Key Differentiator
It’s no secret that traditional, legacy approaches to endpoint security are becoming outdated and less effective. Blacklist-based malware protection simply can’t keep up with the staggering numbers of new malware variants.
This has created a market opening that “next generation” anti-virus providers are more than happy to fill. And in this brave new world of endpoint security, it’s improved threat detection accuracy and automatic containment measures that will dictate which providers lead the pack, says Forrester.
However, traditional anti-virus providers “have not taken this lying down,” Forrester researchers say. Many legacy AV providers are now modernizing their products by acquiring new technologies, and augmenting their own.
For more information, check out the full report, available here.



















