Are You Neglecting Your Enterprise’s IoT Security?
Recently, endpoint security solution provider Trend Micro released the results of their research survey into enterprise-level Internet of Things (IoT) devices. The study raises the question: are you neglecting your enterprise’s IoT security?
According to the Trend Micro study, only about 50% of enterprise-level IT security decision-makers believe the IoT is a security vulnerability—that an IoT attack poses a threat to their business. 43% consider IoT security an afterthought in their IoT deployment strategies.
Yet simultaneously, the stakes for neglecting your enterprise’s IoT security have never been higher. Trend Micro found that 52% of enterprises say that a loss in customer trust is the top consequence of an IoT data breach, with monetary losses coming in second (49%). 63% of respondents agree IoT-related cybersecurity threats are increasing, especially over the past year; enterprises have experienced an average of 3 connected-device attacks over that time frame.
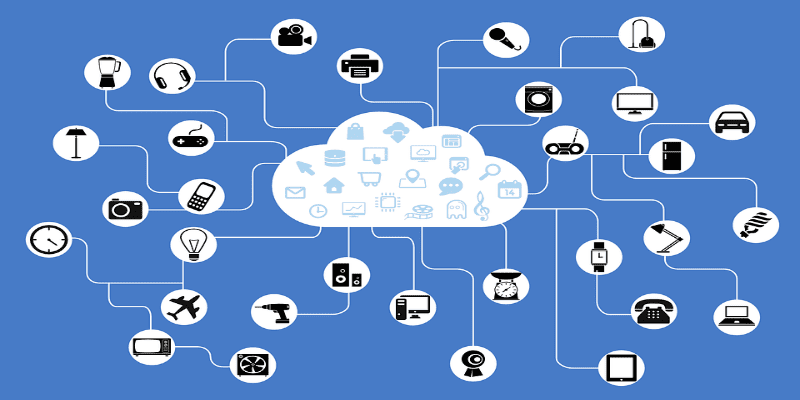
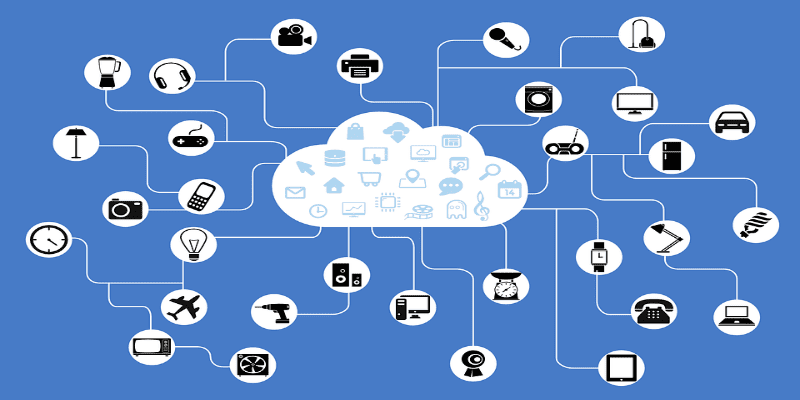
The enterprise IoT attack surface is also growing. The average enterprise has 16,000 IoT devices connecting its networks every day, according to a Ponemon study. But what does this all mean?
What Neglecting Your Enterprise’s IoT security Could Mean
The discrepancy between IoT threat knowledge and action could mean that neglecting your enterprise’s IoT security opens a quiet, unmonitored attack vector into your networks.
We here at Solutions Review have written about it before but it bears repeating—IoT devices are generally not designed or manufactured with endpoint security in mind or in any way involved in the manufacturing process.
Even if IoT manufacturers do give some consideration to cybersecurity, the security firmware they install is often comparatively pitiful to what they actually need to stand up to digital threat actors. Moreover, IoT security is difficult to update, receiving only infrequent patches at best. IoT connections to your enterprise network may make them invisible to your endpoint security or SIEM solution.
In other words, they are almost the perfect attack vector for the digital threat actor.
The Mirai botnet attack—which shut down Internet access on the American east coast—is the most drastic but by no means the only example of an IoT attack at its worst. IoT attacks can use unsecured devices to spoof Wi-Fi connections and directly access your network, use them as a launch pad to steal shared data, use them as an entryway for malware, ransomware, or cryptocurrency miners.
This could apply to any IoT device. Perhaps the most famous example in the present time is the casino hit with a financial IoT attack via a smart fish tank. But Ken Munro of Pen Test Partners demonstrated during his Identiverse Keynote Speech that hackers could steal a Wi-Fi password through a smart kettle. He also demonstrated that hackers could hold physical heating systems for ransom through similar tactics.
Clearly, neglecting your enterprise’s IoT security is not a viable option.
Take Your Enterprise’s IoT Security Seriously
Here’s how to stop neglecting your enterprise’s IoT security:
- Know how many IoT devices are connecting to your enterprise network. This may require a centralized control dashboard.
- Limit the number of IoT devices that are allowed to access your network, and when making purchasing decisions pick devices that can be updated remotely.
- Select IoT devices that can fit into your security platform, and make security a primary consideration in your IoT deployment plans.
- Encrypt and monitor all IoT devices, and turn them off if you aren’t using them.
Final Thoughts
Kevin Simzer, Chief Operating Officer at Trend Micro, put it best in a statement on their survey: “IoT systems are the future for businesses and many new types of connected devices are being introduced to corporate networks.
“While this is beneficial for business operations, the embedded operating systems of IoT devices aren’t designed for easy patching, which creates a universal cyber risk problem. The investment in security measures should mirror the investment in system upgrades to best mitigate the risk of a breach that would have a major impact on both the bottom line and customer trust.”
Trend Micro surveyed 1,150 IT and security decision-makers around the world. You can read more about their findings here.
Other Resources:
IoT Endpoint Security Best Practices For Enterprises
What’s the Worst that Could Happen to your Enterprise’s IoT Devices?
3 Questions on the Internet of Things (IoT) with Mark Cooper of PKI Solutions
Live from the 2018 Identiverse Conference in Boston, MA (Tuesday)
Gartner’s 2018 Magic Quadrant for Endpoint Protection Platforms (EPP): What’s Changed?
4 Tips For Endpoint Security Solutions (That Everyone Forgets)
Endpoint Security Advice for the CISO on the Go!
Endpoint Security vs Legacy Antivirus: What’s the Difference?
Comparing the Top Endpoint Security Vendors — Solutions Review
Answering the Top 4 Enterprise Endpoint Security Questions
Endpoint Detection and Response (EDR): The Way of the Future?
What Can We Expect for the Future of Endpoint Security?





















