North Korea Hacks 140,000 Seoul Computers, Steals Defense Plans
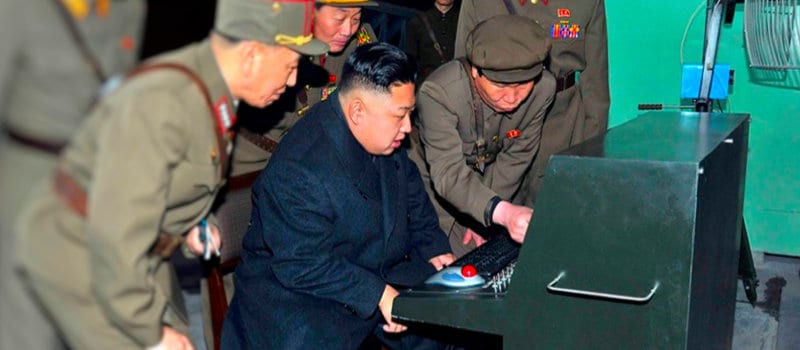
“PWNED” – Kim Jong-un
In popular culture, North Korea isn’t exactly known for technological prowess. The hermit kingdom and last bastion of true Stalinism is frequently lampooned for its outdated tech and for its general insanity. But while we’ve been laughing Kim Jong-un and Co. have been hard at work.
Now that hard work appears to have paid off, because North Korean hackers have breached over 140,000 computers at 160 South Korean companies and government agencies, stealing some 42,000 documents in the process, according to the South Korean National Police Agency.
The attacks began all the way back in 2014 but went unnoticed by Korean authorities until February of this year. Hackers got into the South Korean companies’ networks by attacking a popular network management software, which has remained unnamed by South Korean officials. Once inside the targeted networks, the hackers laid low, presumably in preparation for larger, more coordinated attacks—a familiar tactic that has been used in several recent large-scale attacks, such as the hack of the US Office of Personel Management last year.
Compare Top Endpoint Security Providers with the 2016 Endpoint Security Buyer’s Guide.
- 24 Vendor Profiles and Capabilities References
- 10 Top Questions for Buyer’s
- Complete Market Overview
Once inside the targeted networks, the hackers laid low, presumably in preparation for larger, more coordinated attacks—a familiar tactic that has been used in several recent large-scale attacks, such as the hack of the US Office of Personel Management last year.
Of the 42,000 documents stolen, some 40,000 were defense related. According to Reuters, affected documents included blueprints for the wings of the American-made F-15 fighter jet.
That sounds like a pretty big deal, but South Korean officials have tried to play it down. According to a Defense Ministry official, none of the materials stolen were classified, and representatives of two affected organizations have publically stated that the stolen documents were not classified.
Though IP Addresses used by attackers point to their country, North Korean authorities have denied any knowledge of the attack.



















