ShadowBrokers Release More Data, Hint at Exploits Stolen From NSA
 The anonymous hacking group known as ShadowBrokers has once again publically posted data that it claims to have obtained by hacking a notorious NSA-linked cyber-espionage team known as the Equation Group.
The anonymous hacking group known as ShadowBrokers has once again publically posted data that it claims to have obtained by hacking a notorious NSA-linked cyber-espionage team known as the Equation Group.
ShadowBrokers burst onto the #InfoSec scene in grandiose fashion back in August, when the group posted a 300MB cache of so-called “cyberweapons” stolen from the Equation Group, a hacking team that many security researchers believe to be a part of the NSA’s elite Tailored Access Operations (TAO) unit.
In a statement posted on a Tumblr page, which has since been removed, ShadowBrokers offered to sell off those “cyberweapons” in a bitcoin auction to the highest bidder. As proof, the ShadowBrokers released an unencrypted sample with 300 megabytes worth of exploits designed to target various networking appliances from companies like Cisco and Fortinet. ShadowBrokers then started the bidding for the rest of their cyber-armory at approximately $500 million USD.
Now, ShadowBrokers has released a new document from their trove of ill-gotten security goods.
Aptly titled Trick or Treat?, this new release contains configuration data on an Equation Group toolkit possibly used by the espionage team to breach Sun Solaris servers, which were then used to stage the exploits and carry out attacks for a decade between 2000 and 2010.
Data in the document includes 352 IP addresses and 306 domain names in 49 countries which appear to have been used for hosting the alleged NSA exploit tools, according to an analysis of the data from pen-testing firm Hacker House.
Infected hosts included 32 .edu domains and 9 .gov associated domains, according to Hacker House. The majority of the affected servers were in the APAC region—primarily in China (56 hosts), Japan (41 hosts), and Korea (41 hosts). Spain, Germany, and India rounded out the top five with 25, 17, and 16 hosts, respectively.
The heavy focus on the APAC region was most likely chosen to “hinder attribution and may have been used as a staging ground for further attacks,” says Hacker House.
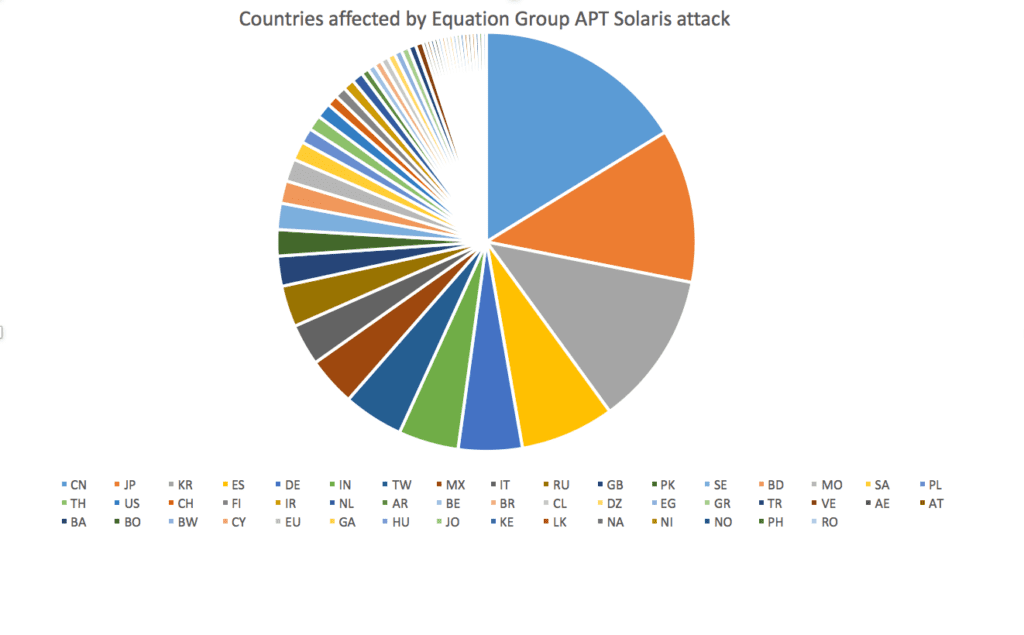
Via Hacker House
While IP addresses and domain names for infected hosts may not be the “cyber weapons” that ShadowBrokers initially promised, they do offer a glimpse at the files in the hacker group’s possession. such as a potential toolkit for breaching Sun Solaris servers.
By releasing these snippets, the ShadowBrokers have let the world know that they have more data and more exploits to leak, and, in explicit terms, that they want to be paid for it—the password for this data dump was “payus.”
But while the ShadowBrokers are obviously motivated by financial gain, they also haven’t been afraid to get political.
In the post announcing this latest leak, the ShadowBrokers bemoaned, in perplexing cartoon-villain faux Russian-English, the US Government’s foreign policy, positions on cybersecurity, and even the impending election.
“Amerikanskis is still thinking “one person, one vote”?,” the posts taunts. “Money isn’t corrupting elections, politics, govenments?”
In an article posted back in August, when ShadowBrokers’ Tumblr post showed similar grammatical errors, linguistics expert Shlomo Argamon claimed that ShadowBroker is a native English speaker masquerading as a non-English speaker.
“The texts contain a variety of different grammatical errors that are not usual in the English of US native speakers,” Argamon says in his analysis, suggesting that the ShadowBrokers used these mistakes to cast suspicion on foreign nationals such as the Chinese or Russians.
“While no one of these factors is dispositive, the cumulative effect of these multiple lines of evidence leads to the conclusion that the author is most likely a native speaker of US English who is attempting to sound like a non-native speaker by inserting a variety of random grammatical errors.”


















