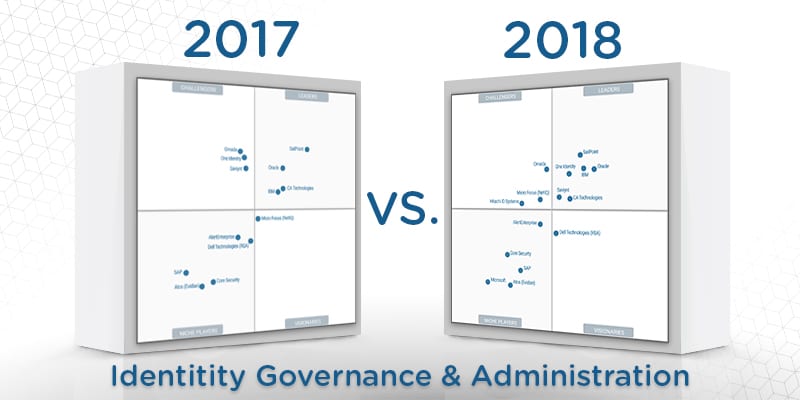
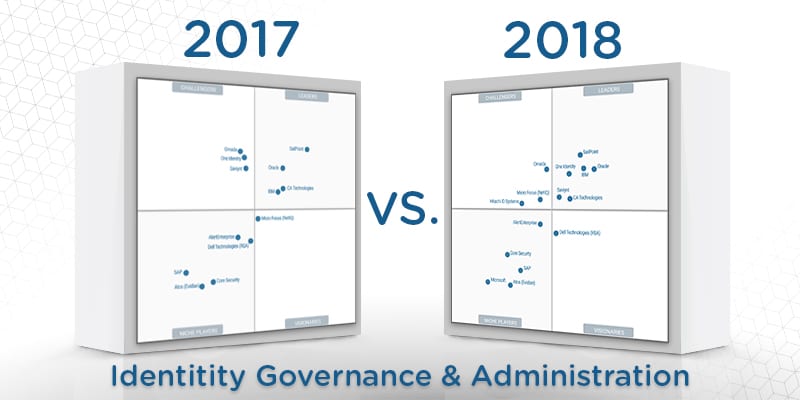
2018 Gartner IGA Magic Quadrant: What’s In a Vision(ary)?
What makes a visionary solution provider in identity governance and administration (IGA)? What are the key capabilities indicative of true foresight in the IGA realm? What features should enterprises value in their long-term digital identity and cybersecurity planning?
According to the 2018 Gartner IGA Magic Quadrant, a Visionary vendor offers “products that meet many IGA client requirements, but may not have the means (such as budget, personnel, geographic presence, visibility and so on) to execute as Leaders do.” However, the word “visionary” strikes us at Solutions Review with a very different meaning. To us, a visionary can see beyond the current trends in IGA to the future—whether glittering or grimy—of digital identity, role management, and cybersecurity compliance.
With that idea in mind, we have to ask: what can the Visionaries in the 2018 Gartner IGA Magic Quadrant teach us about IGA best practices? What should enterprises value in their identity solutions? Can the 2018 Gartner IGA Magic Quadrant point us in the right direction?
That last question is perhaps more relevant here than on other Magic Quadrants, as the 2018 Gartner IGA Magic Quadrant only named one Visionary: Dell Technologies (RSA). However, we may be able to still learn best practices from the Niche Players (AlertEnterprise, Core Security, SAP, Microsoft, and Atos) and Challengers (Omada, MicroFocus, and Hitachi ID Systems).
Here are the key takeaways on what the 2018 Gartner IGA Magic Quadrant selections might mean for the future of enterprise IGA solutions:
Get Your (Cloud) Deployment Right
The 2018 Gartner IGA Magic Quadrant recognizes that deployment is a critical issue for its titular solution. Traditional deployments can be resource-intensive, time-consuming, and frustrating. Perhaps that the MQ is singling out cloud deployments from their IGA solution providers is indicative of a shift to new priorities and expectations. Enterprises should weigh how an IGA solution deploys before making their selection, looking for a reasonable timeframe and ease on your (most likely overworked) IT security team.
Additionally, Gartner seems to paying special attention to IGA in relation to the cloud, especially concerning cloud hosting, cloud architectures, and cloud fulfillment as applies to applications. This suggests that Gartner and the IGA solution providers alike recognize that the recent wave of enterprise cloud adoptions and digital transformation is more than just a trend. Instead, these adaptations are part of new kind of industrial revolution. Identity solutions need to adapt alongside with them to ensure that role management remains centralized even in a new decentralized business paradigm.
If your enterprise is considering an IGA solution, make sure that it can operate via the cloud so that your potential scalability is left unhampered when you do decide to digitally transform. IGA solutions are difficult to replace, and if your solution is only on-premises it can make for far more headaches in the future.
Managed Services Becoming All The Rage
We’ve talked about managed services in our other Visionary articles, and the 2018 Gartner IGA Magic Quadrant is no exception. Managed services can remove the workload burden on IT security teams by remotely handling the role management, compliance reporting, and access request management features. They’ve become more popular lately given the cybersecurity staffing crisis and the stress IT security teams face every day in the wake of that crisis.
Managed services appeal strongly to small-to-medium sized businesses who may not have the resources to employ a dedicated team of IT security professionals to handle the deluge of access requests and role verifications that IGA requirements. However, large and global enterprises should also consider it a factor in their cybersecurity decisions as well; selecting a managed security services provider can allow your internal cybersecurity team to focus on more serious issues such as threat hunting and evaluating potential identity issues.
IGA Integration With Other IAM Features
One last feature the 2018 Gartner IGA Magic Quadrant considers vital to understanding the future of enterprise identity security is that many of the solutions offer integration with other identity tools and solutions. Whether it be IAM analytics, security analytics, and threat intelligence, there is a growing emphasis on creating “all-in-one” solutions.
For your enterprise, you should certainly weigh the integration capabilities of potential vendors before making your selection. Integration issues can create security holes and processing headaches, allowing for orphan accounts or inappropriate access to enterprise assets that could render your enterprise vulnerable to insider threats. IGA is meant to reduce the stress on your IT security, so make sure that your potential IGA solution fits with your other cybersecurity platforms and what additional solutions it can offer. You may save more in the long run.
You can download the 2018 Gartner Identity Governance and Administration Critical Capabilities here.
Widget not in any sidebars




















