Reflection on the 2018 Gartner Magic Quadrant for Identity Governance
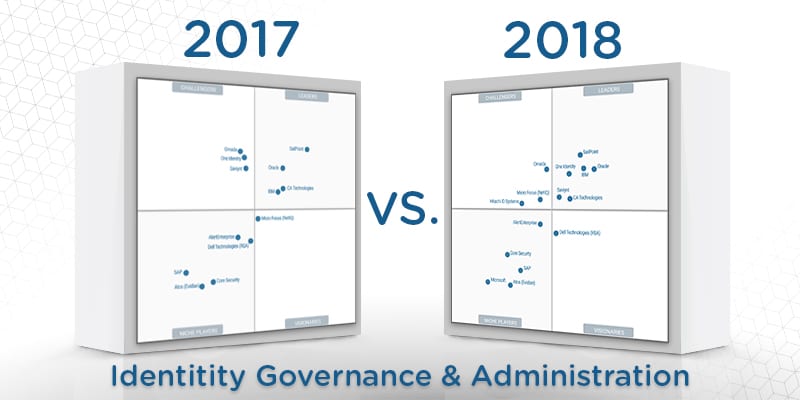
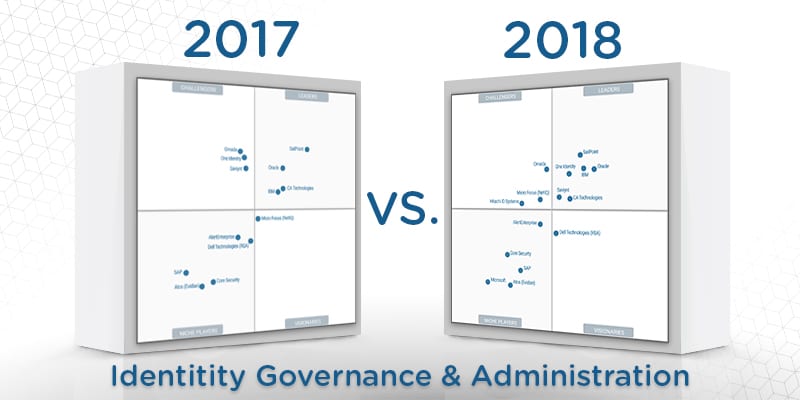
The first quarter of 2018 has come and gone, having seen plenty of cybersecurity innovations, studies, and reports. But few can compare to the arrival of the Gartner Magic Quadrant for Identity Governance and Administration for 2018 in February. This report, written by one of the most respected technology research firms in the world, proved one of the most anticipated in 2018 in the identity management and identity governance marketplaces. It may not be perfect—few reports in cybersecurity are—yet professionals practically leaped in excitement in the wake of its release.
Identity governance is a cybersecurity marketplace with mature solutions, and those solutions are experiencing increased adoption rates by enterprises across the globe. Yet the world keeps turning and what seemed so sure a few months ago may not be so clear now. Therefore, it is important for us to evaluate the accuracy of the 2018 Gartner Magic Quadrant for Identity Governance and Administration. How do their predictions hold up so many months later? How has the speed of digital business and cybersecurity innovations changed their assessments? How do their predictions explain the current state of the identity governance market?
(Editor’s Notes: Some of these question Gartner answered in their recently released 2018 Identity Governance and Administration Critical Capabilities Report, available here).
What is Identity Governance?
The Gartner Magic Quadrant for Identity Governance and Administration isn’t just a set of market predictions and vendor profiles; it’s also an excellent tool for defining this distinct and powerful cybersecurity tool.
Identity Governance is a critical component or subsection in the larger identity and access management field. It is responsible for the distribution and monitoring of roles and permissions within your enterprise’s IT environment. Identity governance can tell you which employees have what access in your network, who is responsible for granting those permissions, and when employees use those permissions to access enterprise assets or databases.
This capability is essential not only for fulfilling regulatory compliance mandates—which it can—but also for protecting your digital assets. Insider threats have a higher chance of success —bringing financial and legal repercussions to your business—if they are allowed to operate in digital darkness. Identity governance prevents that from happening by providing visibility on precisely who can do what and when they do it, allowing your IT security team to adjust permissions on the fly if they constitute a security risk.
Identity Governance: On-Premise or As-A-Service?
One of the most prominent claims in the 2018 Gartner Magic Quadrant for Identity Governance is that on-premises identity governance software is mature, but that the market will be moving heavily towards IGA as-a-service for deployment.
In fact, Gartner predicts that identity governance as-a-service will be the dominant deployment model by 2021, as it can reduce enterprises’ deployment and maintenance costs substantially.
Gartner’s claim has proven difficult to verify at this time. Plenty of identity governance and administration solution providers offer identity governance as-a-service deployment options. However, we could not find any concrete statistics about the comparative rates of adoption for on-premises and as-a-service delivery. This may not be surprising; Gartner admits in their report that as-a-service deployments are still a low percentage of overall IGA deployments. However, given the prevalence and attention enterprises are paying to digital transformation and cloud adoption, then an uptick in identity governance as-a-service deployments would make sense. It would be better suited for a decentralized, cloud-based IT environment.
Some Forethought Required?
According to the 2018 Gartner Magic Quadrant for Identity Governance and Administration, IGA solutions are “sticky”—solutions are difficult to replace and require a serious amount of internal network maintenance and plenty of IT talent on hand to deploy and manage correctly.
Yet their observation can equally apply to other cybersecurity solutions such as SIEM and endpoint detection and response (EDR). Both need the attention of internal IT security teams and continual management to function at optimal levels of performance.
Monitoring appears to be the common theme of all these cybersecurity solutions. Cybersecurity has entered a “monitoring paradigm” that does indeed require human intelligence to run, as traditional set-it and forget-it preventative measures have proven to be inadequate at protecting enterprises on their own.
The question then is whether identity governance and administration is in the same category as SIEM and EDR. All three feature automation as a key capability—which theoretically should relieve some of the burdens on your IT staff—but IGA’s automation is inherent in their solution designs’. It, too, monitors but doesn’t typically have the alarm capabilities of EDR and SIEM, so it may require less attention than those.
This reflection is not meant as a critique of Gartner’s Magic Quadrant for Identity Governance and Administration in any way. We greatly respect their research and insight into cybersecurity technologies. This reflection is merely meant as a companion piece to help enterprises evaluate their selection process for one of the most difficult and important digital decisions you will make. As Gartner themselves point out, it’s a decision that could bring your enterprise security for years to come…or could haunt you.
You can download the full 2018 Gartner Identity Governance and Administration Critical Capabilities Report here.
Widget not in any sidebars