Top 10 Resources for Evaluating Identity Management Solutions

Identity management is a fundamental part of organizational information security, yet too many businesses still rely on username and password combinations, the simplest, oldest form of authentication, to do the job.
But times are changing, and as traditional methods prove dangerously insecure many organizations are looking to modernize their Identity and access management (IAM) solutions and practices. In order to do that, IT workers, CIOs, and CISOs need to conduct extensive research to correctly plan, assess, and deploy the right solution for their organization.
So where should you start? A typical internet search may yield some worthwhile answers, but you’ll likely be spending a lot of time wading through sponsored links to so-called ‘expert’ analysts pushing their own agendas (and products). When it comes to IT buyer’s research, consulting trustworthy independent sources is the name of the game.
With that in mind, we’ve compiled a list of the 10 best buyer’s resources for evaluating Identity Management solutions. Since each organization needs a tool to match up with their own specific use cases, these resources allow researchers to sift through solutions that satisfy a wide range of Identity Management and Governance requirements.
For even more resources, check out our IAM resource library, which features 26 top resources, and is constantly updated.
1. Gartner Magic Quadrant & Critical Capabilities
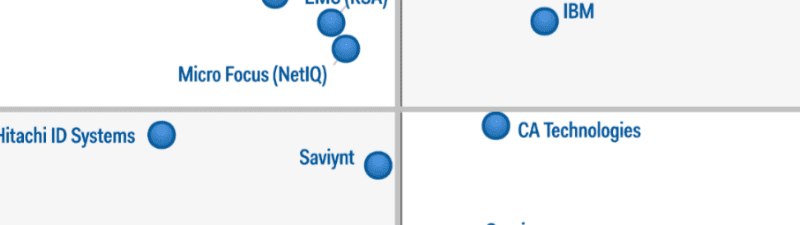 Gartner is the world’s largest information technology research and advisory company, delivering reports and market research studies that assist businesses in making product selection. Gartner is best-known for its Magic Quadrant reports, which rank solution providers based on their ability to execute and completeness of vision. Each Magic Quadrant focuses on a specific market, giving researchers a wide-angle view of the top tools available to them. Gartner currently publishes Magic Quadrants for Identity and Access Management as a Service (IDaaS) and Identity Governance and Administration (IGA). Gartner also offers Critical Capabilities reports, which allow the reader to compare vendors based on specific use cases which relate to their own environments.
Gartner is the world’s largest information technology research and advisory company, delivering reports and market research studies that assist businesses in making product selection. Gartner is best-known for its Magic Quadrant reports, which rank solution providers based on their ability to execute and completeness of vision. Each Magic Quadrant focuses on a specific market, giving researchers a wide-angle view of the top tools available to them. Gartner currently publishes Magic Quadrants for Identity and Access Management as a Service (IDaaS) and Identity Governance and Administration (IGA). Gartner also offers Critical Capabilities reports, which allow the reader to compare vendors based on specific use cases which relate to their own environments.
2. Forrester Wave Report & Vendor Landscape Reports
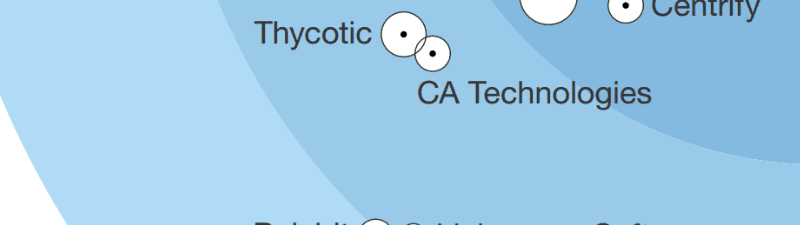 Forrester offers a wide variety of resources to assist business leaders in selecting the right enterprise technology solutions. As one of the most well-established technology research outlets, Forrester is a trusted source of information, offering expansive market studies that encompass a multitude of charts, graphics, and figures. Forrester’s flagship methodology lies in the company’s ever-evolving quarterly Wave reports as well as their in-depth vendor landscape reports. Forrester currently offers Wave reports for IDaaS, B2E Cloud IAM and Privileged Identity Management (PIM), as well as Vendor Landscape reports for Identity Management for the Internet of Things, and a Market Overview for Consumer Identity and Access Management.
Forrester offers a wide variety of resources to assist business leaders in selecting the right enterprise technology solutions. As one of the most well-established technology research outlets, Forrester is a trusted source of information, offering expansive market studies that encompass a multitude of charts, graphics, and figures. Forrester’s flagship methodology lies in the company’s ever-evolving quarterly Wave reports as well as their in-depth vendor landscape reports. Forrester currently offers Wave reports for IDaaS, B2E Cloud IAM and Privileged Identity Management (PIM), as well as Vendor Landscape reports for Identity Management for the Internet of Things, and a Market Overview for Consumer Identity and Access Management.
3. Solutions Review Buyer’s Guide & Fact Book Reports
 Solutions Review has engineered three tools for assisting buyers in their search for Identity Management tools. The Buyer’s Fact Book offers a high-altitude snapshot of the top 28 IAM vendors with vital data on each company’s maturity, longevity, business model, size, geographic reach, workforce, user base, notable clients, and financials, making it easy for companies considering IAM implementations to compare and contrast solutions and find their best fit. Solutions Review also offers a free IAM Buyer’s Guide, further enhancing the ability of the IT professional to make the right product decisions. In using these tools in conjunction, solutions-seekers will be armed with all of the materials they need to ensure selection of the best software for their company. Finally, we recently released a PAM Buyer’s Guide, which hones in on the best practices and solutions for Privileged Access Management use cases.
Solutions Review has engineered three tools for assisting buyers in their search for Identity Management tools. The Buyer’s Fact Book offers a high-altitude snapshot of the top 28 IAM vendors with vital data on each company’s maturity, longevity, business model, size, geographic reach, workforce, user base, notable clients, and financials, making it easy for companies considering IAM implementations to compare and contrast solutions and find their best fit. Solutions Review also offers a free IAM Buyer’s Guide, further enhancing the ability of the IT professional to make the right product decisions. In using these tools in conjunction, solutions-seekers will be armed with all of the materials they need to ensure selection of the best software for their company. Finally, we recently released a PAM Buyer’s Guide, which hones in on the best practices and solutions for Privileged Access Management use cases.
4. KuppingerCole Leadership Compass: Access Management and Federation
 KuppingerCole is an international analyst firm that specializes in offering thought leadership in areas including Identity & Access Management and Digital Transformation. In their Leadership Compass for Access Management and Federation, KuppingerCole’s analysts give an in-depth analysis of 17 major Access Management and Federation vendors, along with insight into major market trends and name market leaders in four categories: Product, Market, Innovation, and Overall. They also offer an IDaaS Leadership Compass Report.
KuppingerCole is an international analyst firm that specializes in offering thought leadership in areas including Identity & Access Management and Digital Transformation. In their Leadership Compass for Access Management and Federation, KuppingerCole’s analysts give an in-depth analysis of 17 major Access Management and Federation vendors, along with insight into major market trends and name market leaders in four categories: Product, Market, Innovation, and Overall. They also offer an IDaaS Leadership Compass Report.
5. TrustRadius Software Reviews
TrustRadius is a review site for business software, helping buyers make better product decisions based on unbiased reviews, many of which that come from the actual end-users themselves. The resource collects reviews that are in-depth and substantive, with every reviewer on the site vetted by the TrustRadius research team before publication. This is important to note so you know the reviews aren’t being submitted by paid actors or vendor marketing teams. In addition, TrustRadius employs a handy algorithm that ensures product scores represent only true customer sentiment by correcting for selection bias.
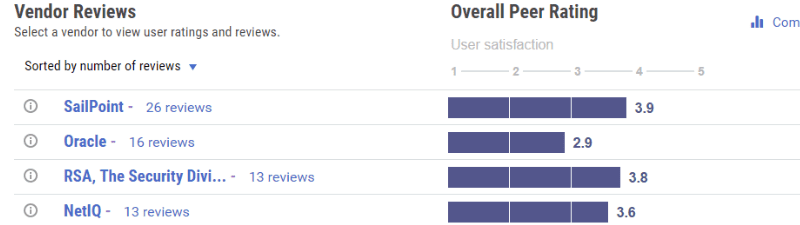
6. Capterra Reviews & Ratings
 Capterra is a great resource for those who are unfamiliar with the current state of the enterprise Identity Management market. It provides a simple way for readers to peruse vendors, read reviews and ratings, and gain a better understanding as to who the key players are. Capterra’s Add to Compare feature is handy for measuring solutions up against one another if there is a specific functionality on your wish list. What Capterra lacks in terms of sophisticated graphics and visuals it makes up for in ease-of-use.
Capterra is a great resource for those who are unfamiliar with the current state of the enterprise Identity Management market. It provides a simple way for readers to peruse vendors, read reviews and ratings, and gain a better understanding as to who the key players are. Capterra’s Add to Compare feature is handy for measuring solutions up against one another if there is a specific functionality on your wish list. What Capterra lacks in terms of sophisticated graphics and visuals it makes up for in ease-of-use.
7. Gartner Peer Insights
 Gartner Peer Insights is Gartner’s answer to the crowdsourced review site—a crowdsourced review site of their own. With their Peer Insights program, Gartner is trying to present the collective experiences of thousands of qualified (and verified) tech buyers and end users who have already gone where you are headed. Perhaps most importantly, Gartner’s Peer Insights democratizes the evaluation process, allowing for vendors not typically included in Magic Quadrants and Critical Capabilities reports due to their stringent requirements. Gartner’s Peer Insights on Identity Governance and Administration features 113 reviews on 19 vendors—far more than considered in the Magic Quadrant and Critical capabilities reports.
Gartner Peer Insights is Gartner’s answer to the crowdsourced review site—a crowdsourced review site of their own. With their Peer Insights program, Gartner is trying to present the collective experiences of thousands of qualified (and verified) tech buyers and end users who have already gone where you are headed. Perhaps most importantly, Gartner’s Peer Insights democratizes the evaluation process, allowing for vendors not typically included in Magic Quadrants and Critical Capabilities reports due to their stringent requirements. Gartner’s Peer Insights on Identity Governance and Administration features 113 reviews on 19 vendors—far more than considered in the Magic Quadrant and Critical capabilities reports.
8. Tom’s IT Pro Reviews and Guides
 Tom’s IT Pro is a well-known resource for enterprise technology professionals looking for best practices and news, but the site also provides in-depth buyer’s guides and resources on a wide variety of topics, all available without fee or registration. In their lengthy guide to IAM, Tom and co. explain key features of IAM and identify their ‘Top Picks’ in the marketplace. Tom’s IT Pro also features an extensive guide to Identity Management using Microsoft’s Active Directory.
Tom’s IT Pro is a well-known resource for enterprise technology professionals looking for best practices and news, but the site also provides in-depth buyer’s guides and resources on a wide variety of topics, all available without fee or registration. In their lengthy guide to IAM, Tom and co. explain key features of IAM and identify their ‘Top Picks’ in the marketplace. Tom’s IT Pro also features an extensive guide to Identity Management using Microsoft’s Active Directory.
9. SlideShare
 SlideShare is a great tool for uncovering insights related to just about any software category. The resource offers a vast library of slideshows, presentations, videos, infographics and more, allowing researchers to uncover best practices, tips of the trade, and important information on some of the top software solutions for enterprise technology professionals. Build your knowledge quickly from concise, well-presented content from top experts. Instead of scrolling through pages of text, you can flip through a SlideShare deck and absorb the same information in a fraction of the time. The resource touts more than 18 million uploads in 40 content categories and is one of the top 100-most visited websites in the world.
SlideShare is a great tool for uncovering insights related to just about any software category. The resource offers a vast library of slideshows, presentations, videos, infographics and more, allowing researchers to uncover best practices, tips of the trade, and important information on some of the top software solutions for enterprise technology professionals. Build your knowledge quickly from concise, well-presented content from top experts. Instead of scrolling through pages of text, you can flip through a SlideShare deck and absorb the same information in a fraction of the time. The resource touts more than 18 million uploads in 40 content categories and is one of the top 100-most visited websites in the world.
10. The Definitive Identity Management Glossary
Having a hard time keeping up with Identity Management jargon? We’ve got you covered. Solutions Review’s A to Z Identity Management glossary is the most complete Identity Management glossary of terms available on the web. With over 70 terms defined, this resource is sure to help keep you hip to all the latest and greatest lingo and acronyms. The Identity Management market is undergoing a major evolution, making terminology and vocabulary an integral part of keeping up to date with all the changeover.