Building a Security Operations Center
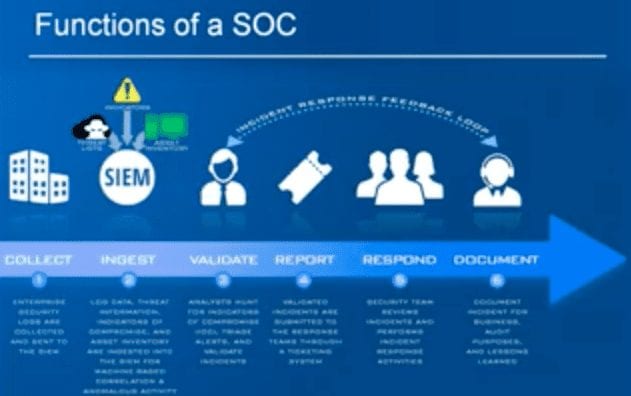
Today’s enterprises have a variety of security tools to help combat the ever-growing cyber threats posed to their businesses. As investment in security has increased, the complexity of managing, monitoring, and extracting value from these tools has also increased – not to mention the cost of resources. A Security Information and Event Monitoring (SIEM) system is often used to collect information from these disparate systems for centralized review and action. A SIEM forms the core of a Security Operations Center (SOC). A SOC is a combination of tools, processes, and personnel which is dedicated to discovering, triaging, and investigating security incidents within an organization.
Building a SOC is not simply implementing a SIEM solution – it is the evolution of it. A properly implemented SOC can greatly reduce time to remediate security issues, provide more effective threat detection, and provide contextual data which allows analysts to appropriately prioritize incidents based on the severity of the threat and the business value of the affected assets.