Neil Weitzel of Cygliant Discusses Meltdown and Spectre
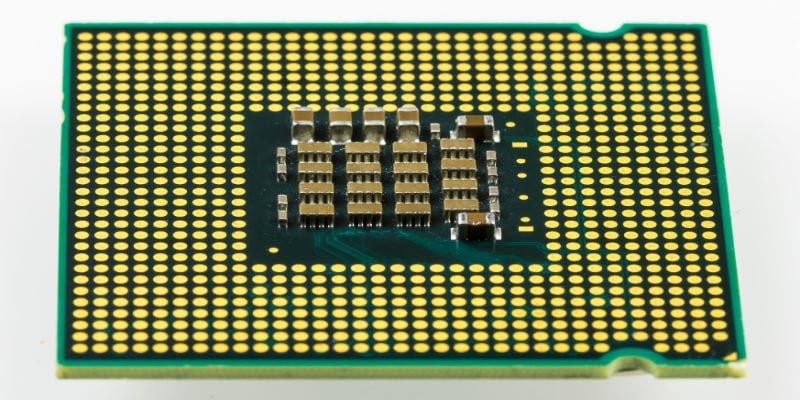
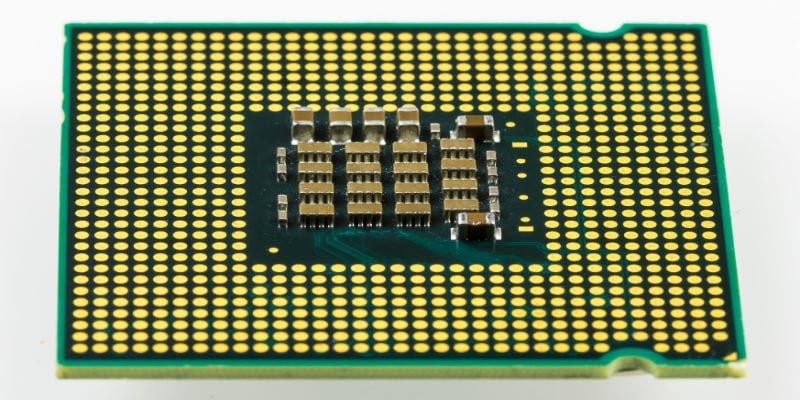
Intel’s announcement of long-standing microprocessor security flaws—nicknamed Meltdown and Spectre—have sent panic through the cybersecurity world. The revelation that speculative execution—the process by which microprocessors anticipate future operations and pre-run them accordingly— left nearly every computer and endpoint vulnerable to malicious code accessing their memory banks opened a floodgate of questions from all sides.
To help us make sense of the severity of this news, we spoke with Neil Weitzel, Director of Security Research at Boston-based SIEM vendor Cygilant. Here’s a transcript of our conversation, edited for readability:
Solutions Review: Intel has been downplaying the severity of Meltdown and Spectre as threats. Do you agree with them that the dangers are being over-exaggerated? Or is this far more serious than Intel wants to admit?
Neil Weitzel: While a critical vulnerability, the likelihood of an exploit occurring is low. Most attackers would need to be state-sponsored or highly technical—think stuxnet.
SR: Intel and other microprocessor manufacturers are refusing to call this a design flaw. Is it, in your opinion? Should these issues have been discovered much sooner than they were?
NW: This is a design flaw because our unprivileged processes are address and access privileged processes or cache. These issues may have been known for some time, but this is the first public disclosure to this magnitude. Just because a vulnerability is made known to the public one day doesn’t mean it hasn’t been available or used previously.
Yes, this should have been discovered and steps toward remediation should have been taken sooner.
SR: Patches are being released daily to alleviate Meltdown and Spectre. What do you make of these patches? Will they be enough to solve the problem?
NW: The patches address the hardware vulnerability from a software perspective. This means the design flaw and vulnerability are still available; the software is merely treating a symptom, not the actual problem.
The patches mitigate the Meltdown ability by removing much of the addressable, privileged processes address from the userspace. Spectre is being patched by attempting to isolate branch predictions to one process, but this is a bit trickier.
SR: There have been increasing reports that the patches released aren’t integrating with anti-virus software. Does this foretell of future security problems, or is this a minor issue?
NW: This is because many anti-virus programs run in privileged processing space; changing how the operating system or applications utilize memory and processes may cause the anti-virus software to create a system malfunction. Similarly, the major anti-virus vendors are working with the vendors that are patching applications and software to ensure their products will work properly after an update.
SR: How do you foresee the discovery of Meltdown and Spectre changing the way microprocessors are manufactured? Or how anti-malware/endpoint security/SIEM solutions are designed in the future?
NW: We will likely need to take these types of vulnerabilities into account when we design systems. We need to keep sensitive workloads on machines and systems [separate from] non-sensitive workloads. Similarly, we need to educate end-users on how they may introduce these exploits by accidentally running nefarious code or applications—through unsolicited attachments and portable media storage, for example.
As for SIEM, [it will be about creating] a whitelist of known-good processes and connections—web access, application services—and [using] it to audit what is currently running on your systems. Anti-virus and malware solutions may attempt to monitor process sharing and reading in future iterations, much like how mobile intents are handled in Android.
Thanks again to Neil Weitzel for speaking with us! You can find out more about Cygilant here.
Neil Weitzel has 10 years of professional technology experience. In addition to being an expert application penetration tester Weitzel is also an excellent instructor and leader: outside of Cygilant, he is an active member of the security community by delivering lectures at DEF CON, OWASP and Denver Security Meet-ups.
Widget not in any sidebars



















