Why Network Packet Captures Should Matter to CIOs and CISOs
So what are network packet captures? Why do they matter to modern SIEM processes and network security? Why should enterprise CIOs and CISOs care about them?
To answer these questions in-depth, we spoke with Jason Walls. Mr. Walls serves as Director of Technical Marketing for CloudShark, a QA Cafe LLC product. CloudShark offers a collaboration platform for packet analysis, troubleshooting, and investigation.
Take it away, Mr. Walls!
Widget not in any sidebars
Why Network Packet Captures Should Matter to CIOs and CISOs
By Jason Walls
Network security has never been more important; network visibility demands have seen a huge increase as networks become virtualized and more complex.
Currently, Network and Security Operations Center (NOC and SOC) teams count every minute when troubleshooting performance problems or hunting down malicious activity. As technology has improved, more organizations have turned towards analytics, AI, and automation in order to manage this complexity and reduce dwell time.
Many of these tools are based around high-level “dashboard” style systems for network visibility or security monitoring. For example, automated Intrusion Detection Systems (IDS) that apply threat rules to flag malicious activity have become the norm, and are becoming more advanced every day. Indeed, the competition is high as security software companies (“as a service” or otherwise) seek to capture this ever growing and important market.
The gains achieved by CIOs through automation and analytics cannot be understated. However, the need for teams to view and analyze network data directly becomes even more critical as automation becomes relied upon more heavily.
This information, in the form of network packet captures, provides the evidence and detail necessary for experts to conclusively resolve issues. Expertise in capture analysis, however, is an esoteric field, and often overlooked by CIOs and CISOs when considering their entire IT or security workflow. Properly realized as the valuable resource they are, giving your teams easy access to packet captures will have your teams solving problems faster and more reliably.
What are Network Packet Captures?
Network packet captures, colloquially known as “pcaps”, are a standardized way to record network data from a network interface.
The “pcap” term comes from the file format generated by the “libpcap” library, which is still used today by nearly any tool that generates network traces. Pcaps contain a record of all of the packets that traversed a given interface, plus additional metadata to aid the use of analysis tools. For example, applications that generate packet captures include tcpdump and Wireshark.
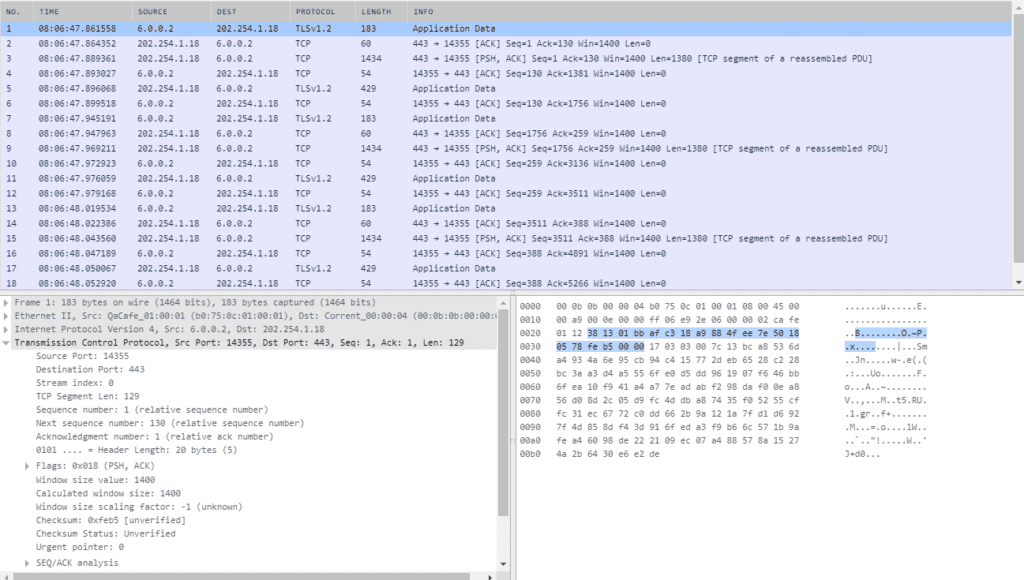
Example of Packet Capture Data via a CS TraceFrame Window
Network visibility and security monitoring tools can include the ability to generate pcaps either as part of their automated processes or when specifically tasked to do so by a user. The capture generation libraries and applications often include the ability to use filters that help capture packets that are of interest, reducing the “noise” for later analysis.
Still others generate full captures of line-rate data, using massive amounts of storage to ensure nothing is missed. This latter is usually used in high-risk industries that have rigorous compliance standards.
From Automation to Workflow—Why Do Captures Matter?
Though network visibility, performance, and security monitoring tools have become better at providing automated feedback to NOC and SOC teams, they do not always provide all of the information necessary to correctly identify, resolve, or report on issues.
All of the information provided has been interpreted in some way by the application. They don’t necessarily show “what’s on the wire,” and differences in how that information is interpreted require analysts to dive deeper to get the real answers.
Uncovering Hidden Performance Issues
In network performance monitoring, while automated tools can tell you which systems or applications may be suffering from performance issues, the “why” can be hidden within the network data itself.
For example, the highly performance-sensitive networks in financial trading can see drastic effects from network “microbursts,” when systems send data inconsistently, overwhelming network equipment in ways that can’t be identified without looking at packets at the microsecond level.
In enterprises, the network (and as a result, IT departments) can get blamed for bad experiences of end users in the organization. With an analysis of the packet captures, teams can demonstrate that it was, in fact, “not the network,” but a poorly designed application or service that is impacting performance.
Accurate Security Resolution and Reporting
Packet captures can make the resolution of performance issues vastly more efficient, but they are absolutely critical to security analysis and threat hunting. An event starts with a security alert, but security alerts are only part of the story. Network packet captures can aid in:
* Eliminating False Positives
IDS systems often rely on standardized threat rules that have been curated by the industry. These rules tend to cast a wide net, looking for anything that might be considered dangerous. Sometimes, this can result in a false positive—a threat alert that turned out to be benign. Having analysts look at the pcaps after the fact can help to eliminate these false positives, allowing the team to tweak the rules or keep track of the issue should it happen again.
* Uncovering Well-Hidden Attacks
Some forms of attack can’t be detected by an IDS. For example, quirks in TCP or differences in the way hosts and monitoring applications handle network data can allow attackers to hide their activity, or trick browsers into loading malicious websites. Differences in the way that operating systems handle TCP will make attacks like this go unnoticed if an analyst is simply looking at the reassembled data stream.
* Enabling Threat Hunting
The cybersecurity community does a good job updating the open-source threat rules that many IDS’ use. However, new attack vectors are exploited every day, and SOC teams go through the threat assessment lifecycle to catch these attacks, report them to the organization, and generate new rules for their automated systems, which are sometimes shared back to the cybersecurity community.
An IDS won’t catch activity it doesn’t know about, and packet capture data is the only way to fully identify, investigate, and remediate a new attack. Additionally, they provide the historical data necessary for retrospective analysis—making sure that what happened didn’t happen before, compromising other systems.
Making Packet Captures Available to NOC and SOC Teams
Once an AI tool isolates an issue, pcaps become an integral part of any NOC or SOC workflow, helping them do their jobs more effectively.
For CIO’s and CISO’s, it’s important to make sure that the tools you choose as part of your overall plan not only include the ability to generate packet captures but allow teams to access them and work with them easily.
For developers of network visibility and security monitoring tools, especially those built on automation and analytics, it’s a critical value-add to include pcap visibility in an easily accessible and responsive way that doesn’t force your users to leave your application to work with them—doing so will give you a significant competitive advantage. In the end, a greater awareness of pcaps and encouraging methods of using them will make for better networks and more secure organizations overall.
Thanks again to Jason Walls of CloudShark for his time and expertise! For more information about cybersecurity capabilities and tools, be sure to also check out our SIEM Buyer’s Guide!




















