5 Alternatives to The Gartner Magic Quadrants for IAM


Gartner is one of the loudest voices in enterprise technology— they’re world’s largest information technology research and advisory company, and generally the first source consulted when it comes to evaluating enterprise IT solutions, and enterprise Identity Management is no exception.
But while the Gartner’s flagship Magic Quadrants for IGA and IDaaS are great resources for finding out who the top enterprise Identity Management contenders are, they don’t give a particularly in-depth analysis behind what each solution offers or how they perform across different industries and use cases. And they typically don’t include a very broad spectrum of solutions.
Gartner’s yearly reports don’t exactly move at the speed of business, and you can’t base an entire RFP off of one resource (though I’m sure some do). A well-informed decision requires a well-rounded research process.
Widget not in any sidebars
IT workers, CIOs, and CISOs need to conduct extensive research to correctly plan, assess, and deploy the right solution for their organization.
That means multiple sources—and lots of work. Luckily, we’ve done some of the work for you. Below, you’ll find the top five alternatives to Gartner’s Magic Quadrant reports.
Since each organization needs a tool to match up with their own specific use cases, these resources allow researchers to sift through solutions that satisfy a wide range of Identity Management and Governance requirements.
But should you feel the need for even more resources, check out our IAM resource library, which features 20 top resources, and is constantly updated with the latest and greatest in Identity Management best practices.
Forrester Wave Report & Vendor Landscape Reports
 Forrester offers a wide variety of resources to assist business leaders in selecting the right enterprise technology solutions. As one of the most well-established technology research outlets, Forrester is a trusted source of information, offering expansive market studies that encompass a multitude of charts, graphics, and figures. Forrester’s flagship methodology lies in the company’s ever-evolving quarterly Wave reports as well as their in-depth vendor landscape reports. Forrester currently offers Wave reports for B2E Cloud IAM and Priviliged Identity Management (PIM), as well as Vendor Landscape reports for Identity Management for the Internet of Things, and a Market Overview for Consumer Identity and Access Management.
Forrester offers a wide variety of resources to assist business leaders in selecting the right enterprise technology solutions. As one of the most well-established technology research outlets, Forrester is a trusted source of information, offering expansive market studies that encompass a multitude of charts, graphics, and figures. Forrester’s flagship methodology lies in the company’s ever-evolving quarterly Wave reports as well as their in-depth vendor landscape reports. Forrester currently offers Wave reports for B2E Cloud IAM and Priviliged Identity Management (PIM), as well as Vendor Landscape reports for Identity Management for the Internet of Things, and a Market Overview for Consumer Identity and Access Management.
View resource: Privileged Identity Management Wave Report
View resource: B2E Cloud IAM Wave Report
View resource: Market Overview for Consumer Identity Management
View resource: Vendor Landscape: Identity Management for the Internet of Things
KuppingerCole Leadership Compass: Access Management and Federation
 KuppingerCole is an international analyst firm that specializes in offering thought leadership in areas including Identity & Access Management and Digital Transformation. In their Leadership Compass for Access Management and Federation, KuppingerCole’s analysts give an in-depth analysis of 17 major Access Management and Federation vendors, along with insight into major market trends and name market leaders in four categories: Product, Market, Innovation, and Overall.
KuppingerCole is an international analyst firm that specializes in offering thought leadership in areas including Identity & Access Management and Digital Transformation. In their Leadership Compass for Access Management and Federation, KuppingerCole’s analysts give an in-depth analysis of 17 major Access Management and Federation vendors, along with insight into major market trends and name market leaders in four categories: Product, Market, Innovation, and Overall.
View Resource: Kuppingercole Leadership Compass – IDaaS: Single Sign-On to the Cloud
Gartner Critical Capabilities Reports
 In addition to their Magic Quadrant reports, Gartner also offers the less well-known Critical Capabilities reports, which allow the reader to compare vendors based on specific use cases which relate to their own environments.
In addition to their Magic Quadrant reports, Gartner also offers the less well-known Critical Capabilities reports, which allow the reader to compare vendors based on specific use cases which relate to their own environments.
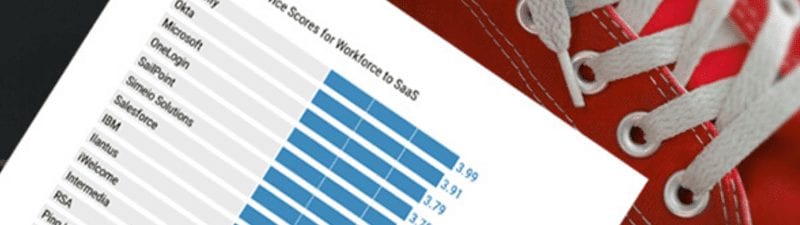
For example, in the 2016 version of their Critical Capabilities report for IDaaS, Gartner takes the 18 vendors that it considers most significant in the worldwide IDaaS market and evaluates the strengths and weaknesses of those vendors against 11 ‘critical capabilities’ and three common use cases for IDaaS. Gartner does not endorse any vendor, product, or service depicted in its research publications.
Gartner defines Critical capabilities as “attributes that differentiate products/services in a class in terms of their quality and performance.”
Gartner rates each vendor’s product or service on a five-point scale in terms of how well it delivers each capability.
Gartner Peer Insights
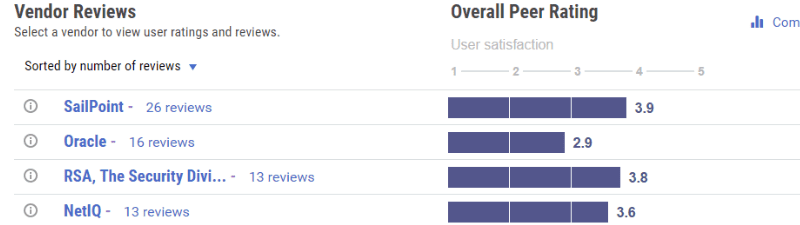 Gartner Peer Insights is Gartner’s answer to the crowdsourced review site—a crowdsourced review site of their own. With their Peer Insights program, Gartner is trying to present the collective experiences of thousands of qualified (and verified) tech buyers and end users who have already gone where you are headed. Perhaps most importantly, Gartner’s Peer Insights democratizes the evaluation process, allowing for vendors not typically included in Magic Quadrants and Critical Capabilities reports due to their stringent requirements. Gartner’s Peer Insights on Identity Governance and Administration features 113 reviews on 19 vendors—far more than considered in the Magic Quadrant and Critical capabilities reports.
Gartner Peer Insights is Gartner’s answer to the crowdsourced review site—a crowdsourced review site of their own. With their Peer Insights program, Gartner is trying to present the collective experiences of thousands of qualified (and verified) tech buyers and end users who have already gone where you are headed. Perhaps most importantly, Gartner’s Peer Insights democratizes the evaluation process, allowing for vendors not typically included in Magic Quadrants and Critical Capabilities reports due to their stringent requirements. Gartner’s Peer Insights on Identity Governance and Administration features 113 reviews on 19 vendors—far more than considered in the Magic Quadrant and Critical capabilities reports.
Solutions Review Buyer’s Guide & Fact Book Reports
 Last but not least, here at Solutions Review we’ve come up with two tools to help buyers in their search for Identity Management tools. The Buyer’s Fact Book offers a high-altitude snapshot of the top 28 IAM vendors, with vital data on each company’s maturity, longevity, business model, size, geographic reach, workforce, user base, notable clients, and financials, making it easy for companies considering IAM implementations to compare and contrast solutions and find their best fit. Solutions Review also offers a free IAM Buyer’s Guide, further enhancing the ability of the IT professional to make the right product decisions. In using these tools in conjunction, solutions-seekers will be armed with all of the materials they need to ensure selection of the best software for their company.
Last but not least, here at Solutions Review we’ve come up with two tools to help buyers in their search for Identity Management tools. The Buyer’s Fact Book offers a high-altitude snapshot of the top 28 IAM vendors, with vital data on each company’s maturity, longevity, business model, size, geographic reach, workforce, user base, notable clients, and financials, making it easy for companies considering IAM implementations to compare and contrast solutions and find their best fit. Solutions Review also offers a free IAM Buyer’s Guide, further enhancing the ability of the IT professional to make the right product decisions. In using these tools in conjunction, solutions-seekers will be armed with all of the materials they need to ensure selection of the best software for their company.
Widget not in any sidebars


















