5 Tips for Setting Up a Security Operations Center (SOC)
For more information on this subject, be sure to check out the “How to Build a Security Operations Center (on a Budget)” whitepaper by SIEM solution provider AlienVault.
Here’s the hard truth: you can’t stop all hacks and attacks on your enterprise. Even the greatest preventative security solution deployed on every endpoint across your corporate network, will let you down eventually. Whether it’s a threat designed to bypass traditional or next-generation threat detection systems, a zero-day attack exploiting an unknown backdoor, or a malicious insider threat, something will break through.
Widget not in any sidebars
When that does happen, securing your enterprise’s data becomes a matter of prompt internal detection and threat removal—processes to reduce an attack’s dwell time on your servers. In turn, this necessitates the constant monitoring of your enterprise’s databases and logs for unusual and possibly malicious activity.
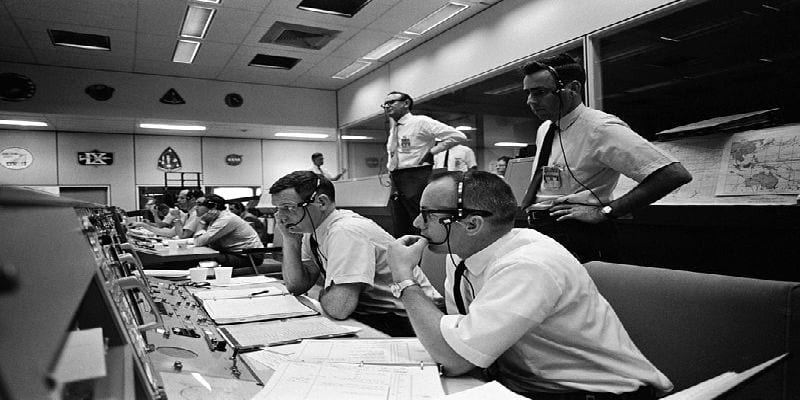
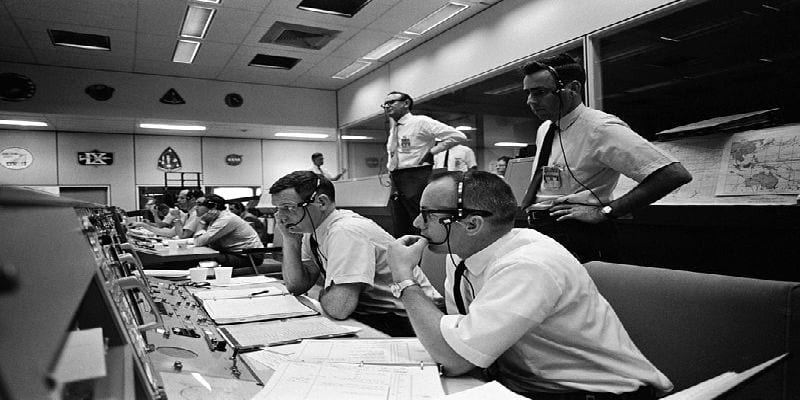
Therefore, it is no surprise that many enterprises have established a dedicated security operations center (SOC) within their organization. An SOC is a facet of your cybersecurity team, sometimes housed in a distinct facility, who evaluate and enforce your security policies and respond to digital incidents.
However, a security operations center can constitute a serious drain on your enterprise’s resources, staff, and time. This applies doubly if you are just setting one up for the first time. Here are some tips to help you establish your own security operations center:
1. Understand What A SOC Does…and What They Shouldn’t Do
A true security operations center staff monitors your enterprise’s endpoints and network, identifies potential security incidents, and handles them promptly and efficiently. They are not the help desk, and nor should they be conflated with said. Doing so will only create unmanageable workloads, undue stress, and potentially allow threats to wreak havoc on your network unchallenged. The help desk should deal with the employee-facing aspects of IT, whereas the SOC should be threat hunting.
2. Provide the Right Infrastructure to Support Your SOC
You may have assembled the best security operations center staff conceived of, but without the correct tools they’ll be virtually helpless. Make sure your enterprise provides them with up-to-date technologies, including:
- Firewalls
- Endpoint Protection Solutions
- Security Information and Event Management (SIEM) Solutions
- Security Probes
- Data Collection Tools
3. Find the Right People for Your Security Operations Center
A good SOC will need a few talented individuals of varying skill sets and focuses, including :
- An alert analyst to monitor the alert queue and the health of security sensors
- An incident responder to perform deep incident analysis
- A subject matter expert who will act as an incident hunter
All of these positions require advanced training in their position-relevant areas, which may include intrusion detection, log reviews, and malware reverse-engineering. Not every organization and enterprise will have these skills on-staff or within their employment reach. Many enterprises will therefore instead enact a hybrid staffing system, teaming the staff they do have with a solution provider to fill in the talent gaps. Furthermore, working with a solution provider will enable the SOC to operate 24 hours a day, 7 days a week—an impossibility for all but the largest enterprises.
On the subject of staffing…
4. Hire a Good Security Operations Center Manager
SOC’s are chaotic by their very nature; enterprises might be hit by numerous incidents a day that require investigation, communication between departments can be difficult or confusing, and crises both external and internal could muddy the duties of the SOC.
Therefore, your enterprise will need an excellent security operations center manager to keep your analysts on task and put out fires when they flare up. An ideal candidate should have good communication skills, project management skills, and a solid understanding of incident response management.
5. Have An Incident Response Plan Ready to Follow
We’ve mentioned before how essential an incident response plan is for enterprises, and that advice is no less true now. An incident response plan can help your security operation center triage detected threats, ensuring a repeatable workflow. It can also establish communication networks between the SOC and the parties that should be informed of a breach when one occurs, including the legal team, the PR office, and relevant regulatory bodies.
These tips are a good place to start, but how do you set up a security operations center without burning through your security budget? How do you properly size your SOC to fit with your enterprise’s needs? Check out this free ebook How to Build a Security Operations Center (On a Budget) by SIEM vendor AlienVault to learn more.




















