How to Get The Most Out of Your Threat Hunting Practices
The current state of cybersecurity can be summarized thusly:
- The previous paradigm was dominated by the idea of threat prevention.
- As digital threat actors have grown more sophisticated and more persistent, enterprises’ IT security perimeter have become more porous.
- Attackers have more attacks vectors and more opportunities to increase their dwell time.
- No preventative measure, no matter how strong, can deflect 100% of attacks.
- Thus the cybersecurity paradigm has shifted from prevention to threat detection and response.
SIEM solutions are perfectly primed to facilitate this widespread refocus on threat detection; they can provide better visibility into enterprise networks, compile, standardize, and correlate disparate security events, alert security researchers to potential threats, and generate logs for compliance. However, IT security teams need to be actively engaged with their SIEM solution in examining the possible threats and finding the legitimate attacks in order to make the most of your solution and its log information.
In other words, your IT security team needs to be threat hunting.
But how do you facilitate the best threat hunting possible? How can your threat hunting work with, rather than against, your SIEM solution? And what talents do your team need to become expert threat hunters?
Here’s what you need to know:
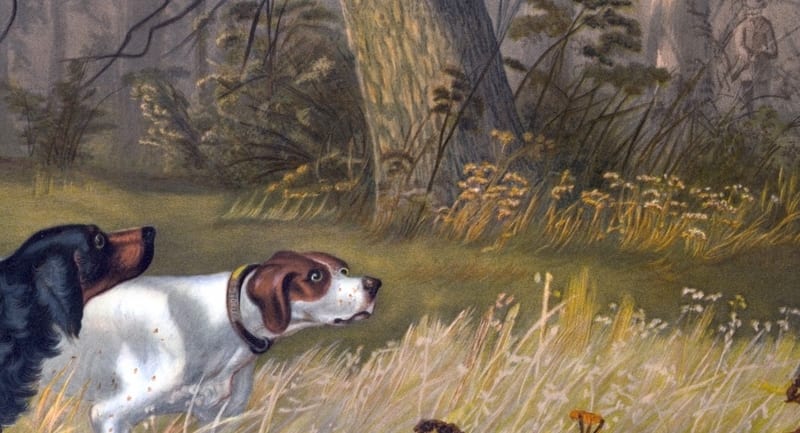
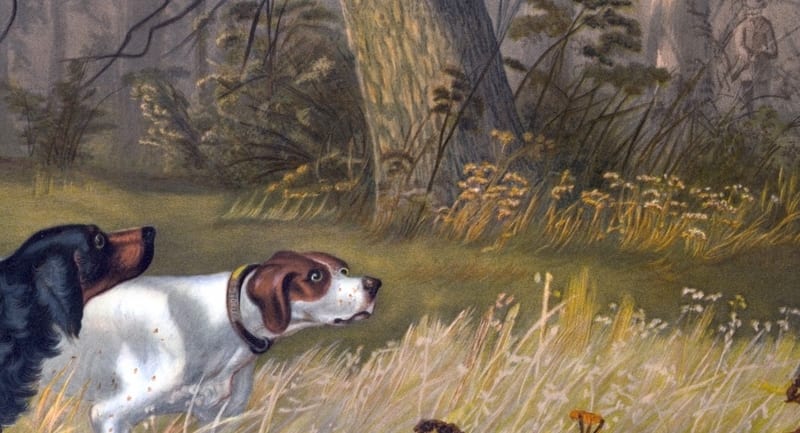
Develop Your Team’s Killer Instincts
We here at Solutions Review constantly warn enterprises to assume that they will be targeted by a digital threat actor rather than thinking it can’t happen to them. A similar principle applies to threat hunting: when in doubt, always assume you have been breached.
SIEM solutions have a reputation (not necessarily undeserved) of generating false positives in their security event correlations. Yet assuming that all of the alerts are false throws the metaphorical baby out with the bathwater. Your team needs to explore the possibility that every alert is a legitimate threat and pursue each with the same energy and with the same critical eye.
In threat hunting, as in real life, you may not always find your quarry. The trail may go nowhere. But if you do not follow each lead, your prey will get away every time.
Train Your Team on What to Look For
It can be difficult at times to recognize what is and isn’t a legitimate attack while threat hunting. Some activities are flagged as suspicious when they are just an unusual business activity or even a regular activity.
However, these activities can be a sign of something nefarious on your network:
- Communications or processing slowdowns
- Unusually consistent byte pattern
- Suspicious Site Interactions
- Failed Login Attempts
- Unexpected Privilege Changes
- Password Dumping Programs
- Exploit or Backdoor Appearances
Make sure your IT security team knows how to recognize these and how to track them down.
Teach What to Do If Your Threat Hunting Finds Something
If your security team’s threat hunting endeavors do find the signs of a legitimate attack, do they know what they need to do next?
You need to make sure that your IT security team has the technology and skills to recognize the full scale of an attack and be able to respond to it accordingly. Your team needs to be able to respond to discovered threats of all varieties, predict what each threat is aiming to do and where it will go in your network, and adapt quickly.
Customizing your existing tools can be an option, but it can be a lengthy process that could hamper your threat hunting efforts. Make sure your SIEM solution is as facilitating to threat hunting as possible to keep the process running smoothly.
If your team can’t close off all of the attack vectors or stop the attack in full, your system will remain compromised for longer and therefore accumulate more damage.
Threat Hunting Begins with a Single Step
Accumulating the right skills and technologies for threat hunting is, of course, important, but threats are coming in every day and from every direction. Waiting for the “perfect team” will result in longer dwell times and unchallenged hackers running rampant on your network.
Your IT security team needs to get started on their threat hunting early. Even if some of them are inexperienced at threat hunting, they will acquire that experience keeping your enterprise safe.
Even the best threat hunters started off fresh-faced. Give your green team the experience they need to become the veterans your enterprise deserves.
Get Proactive
With a SIEM solution on your side, it can be easy to think of threat hunting as entirely reactionary. Your threat hunting team could end up waiting for a security alert to investigate, only then springing into action after a threat has already started attracting attention.
While the temptation to let threats come to you can be powerful, your IT security team should be threat hunting proactively, not reactively. They should be patrolling your networks for any sign of illicit activity or intrusion and taking the steps to shore up your network defenses when they can.
Remember: if your SIEM solution discovers security event information pointing to a threat, that means a threat has already penetrated your network. Your IT team should be doing everything in its power to stop that from happening at all.
Other Resources:
Get Your Employees to Embrace SIEM Best Practices!
4 Tips to Make Data Breach Detection Easier For Your Enterprise
Enterprises: Don’t Become Complacent in Your Cybersecurity!
How to Make Your SIEM Solution Deployment Easier for Your Enterprise
Comparing the Top SIEM Vendors — Solutions Review
How UEBA Can Prevent Insider Threats in your Enterprise
SIEM vs Security Analytics: What’s the Difference?
Should Risk Analytics Bridge the Cybersecurity Talent Gap?
Widget not in any sidebars



















