Juniper Networks Breach May be a Bigger Deal than Originally Thought
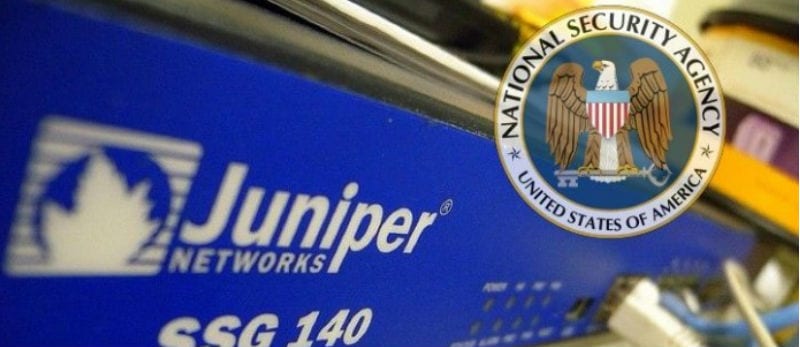
Yesterday, Congressman and chairman of the IT Subcommittee on Oversight Government Reform, Will Hurd wrote in the Wall Street Journal that the recently discovered security breach in the form of unauthorized code at Juniper Networks has officials worried that foreign hackers may have been reading encrypted U.S. government communications for the past three years and demands more serious attention than it has been getting.
On December 17, 2015 it was announced that Juniper had discovered an unauthorized backdoor in its ScreenOS software which allowed outside moderation of network traffic. Hackers could have potentially decrypted information and controlled firewalls. A patch was immediately released to close the backdoor, but there may have been more to it than was initially reported.
According to Hacked.com, a document shared by Edward Snowden revealed that the NSA knew about the Juniper backdoor since 2011 but the extent of the vulnerability is still unknown. The version of ScreenOS that used by the goevenment has not been updated since 2011. There were government agencies affected, but they have yet to be identified, but it is known that several government agencies used ScreenOS.
The news of a security breach in Juniper Networks has been widely known since late last year, with security researchers trying to solve the mystery of how a backdoor like this could have worked. Just a month ago, Kim Zetter from Wired revealed that researchers found suggestions that the NSA may have even been responsible for the backdoor, although it may have been indirect or unintentional.
Nextgov.com reveals that 24 departments and agencies have been asked by the Oversight and Government Reform Committee to provide them with an inventory of their affected ScreenOS Juniper products.
“So that the committee may better understand the extent of the ScreenOS vulnerabilities and related effects on the cybersecurity posture of federal agencies that use” the tools, “please provide the following documents and information as soon as possible,” reads a Jan. 21 letter sent to the departments of Commerce, Defense, State, as well as NASA, the Nuclear Regulatory Commission and the other federal agencies.
Agencies must report whether they used the compromised Juniper programs, how they “discovered the vulnerability and if any corrective measures were taken prior” to deploying a software patch issued Dec. 20, 2015, the program versions used and the date they installed the patch.
The FBI investigated the breach back in December and Juniper said that they has found another security issue that would allow and attacker monitoring VPN traffic to decrypt the traffic.
Juniper is one of the leading 802.11ac wireless vendors and will be greatly affected by this breach.