Are Detection Issues Impairing your Enterprise’s IoT Security?
There are two problems compounding the concerns around IoT security:
- Cybersecurity overall continues to be an afterthought for enterprises (which is a separate issue unto itself).
- IoT security is an afterthought of an after-thought for enterprises.
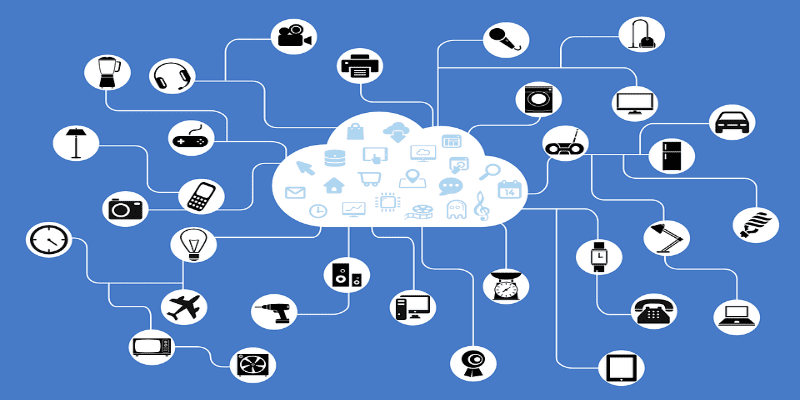
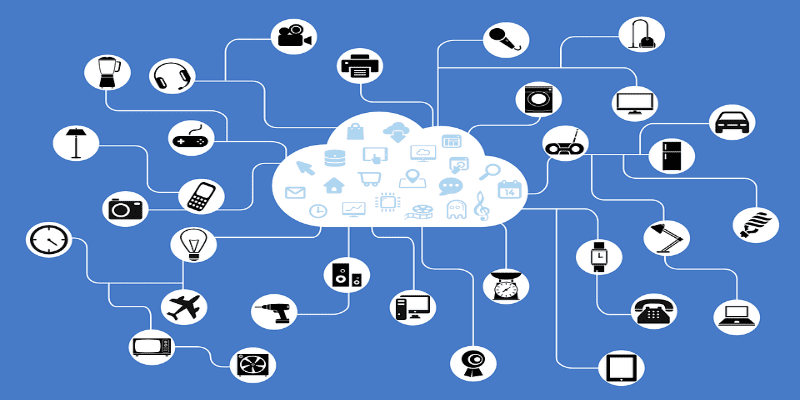
The latter is both deeply concerning and deeply confusing. Internet of Things devices can be exploited to create man-in-the-middle attacks, spy on your network or your analog workplace via connected microphones and cameras, and as holes into the network proper. IoT devices could become part of a botnet and DDoS attack. Indeed, 93% of cybersecurity experts believe the IoT will pose more of a security risk than ever before. Healthcare, Financial, and Energy companies are particularly vulnerable.
The issues behind IoT security concerns are well documented: IoT devices and designed and built with minimal (if any) security and their firmware can be difficult (if not impossible) to update. What isn’t as well documented is the relationship between IoT Security and SIEM. IoT security is traditionally thought of as an endpoint security solution problem; devices can be lost to the perimeter and thus lost to prevention capabilities.
However, IoT security is just as much a SIEM issue as it is an endpoint security issue. SIEM has to get involved in detecting, mitigating, and removing IoT threats as quickly as possible if they have penetrated your devices. If your SIEM doesn’t account for IoT security, possible security events and security holes can continue unnoticed, allowing attackers to dwell.
What could get in the way of SIEM facilitating IoT security?
Is Machine Learning Clouding the Field?
Machine learning is developing into one of the key capabilities of cybersecurity overall. Machine learning essentially creates an automated cybersecurity expert constantly monitoring the network, learning to recognize potential threats through human input, threat intelligence, and through its own experiences. While it may not totally replace human security team members, it is poised to become a major advantage to their operations.
However, machine learning can actually create a lack of transparency throughout your network, as it tends to obscure alert sources—whether those alerts indicate legitimate threats or not. Additionally, machine learning can be dangerously selective about the data they will and will not accept into their learning algorithm. Both of these issues can hide IoT devices from your SIEM detection, leading to potential security issues. Your human cybersecurity team members should make an effort to ensure your IoT devices are thoroughly inspected by your solutions and that IoT events are being processing by your machine learning capabilities.
Alarm Fatigue Limiting IoT Security
False positives alarms are the bane of SIEM and security analytics solutions. While the technology is improving all the time, solutions still struggle at times to distinguish between ordinary events and potential threats or to interpret events accurately. Given how many alerts end up being false positives, there is growing concern of alarm fatigue—cybersecurity teams neglecting alerts because they assume they will be false positives.
Yet your cybersecurity team has to take each alert seriously, especially if they concern your IoT devices. You have to foster a culture that remains energized when tackling security alerts and to recognize how alerts concerning the IoT devices could easily translate into legitimate threats. One strategy might be to prioritize security events or correlations involving IoT devices so that your team is never caught off-guard by an IoT attack.
Report Neglect
In the earliest days of SIEM (which may not seem too long ago to may cybersecurity experts) enterprises sought these solutions out for their compliance reporting capabilities. When the cybersecurity paradigm shifted from prevention to detection, reporting took something of a backseat, but the use of accurate reports has never diminished. You can receive reports on failed logins and intrusion attempts for the same IP address, both of which can be useful for IoT security. Make sure you are collecting reports on your IoT devices to keep them from becoming dark on your network.
Are You Spending Enough on IoT Security?
Experts predict that more than 33 billion records will be stolen in 2023 alone. Experts also predict by 2025 about 80 billion devices (including IoT devices) will connect to the internet.
Coincidence? Correlation? Causation?
Regardless, IoT security must be a critical part of your cybersecurity budget and strategy. If you neglect either your cybersecurity or your IoT security, you invite risk to your whole enterprise. With so many IoT devices being connected to your enterprise’s network, you can’t afford to risk it. IoT Security might seem like a short-term expense, but the long-term savings can’t be argued with!
Other Resources:
5 Tips for Setting Up a Security Operations Center (SOC)
Get Your Employees to Embrace SIEM Best Practices!
4 Tips to Make Data Breach Detection Easier For Your Enterprise
Enterprises: Don’t Become Complacent in Your Cybersecurity!
How to Make Your SIEM Solution Deployment Easier for Your Enterprise
Comparing the Top SIEM Vendors — Solutions Review
How UEBA Can Prevent Insider Threats in your Enterprise
SIEM vs Security Analytics: What’s the Difference?
Should Risk Analytics Bridge the Cybersecurity Talent Gap?
What’s Changed? The Gartner 2017 Security Information and Event Management (SIEM) Magic Quadrant
The 25 Best Security Analytics and SIEM Platforms for 2018
Widget not in any sidebars


















